Introduction: When Compliance Blocks Market Entry
Sometimes, a region’s regulatory compliance rules block businesses from entering a market. That’s exactly what happened with WhatsApp Pay in India. Despite having hundreds of millions of users in the country, WhatsApp couldn’t launch its payments service right away. Indian regulators, including the Reserve Bank of India (RBI) and the National Payments Corporation of India (NPCI), required the platform to meet strict rules around data localization and privacy. Until WhatsApp adjusted its systems to comply, it couldn’t scale its payment offering—giving rivals like Google Pay and PhonePe a big lead.
This example shows how local compliance requirements don’t just affect operations—they can determine whether a product even gets off the ground. As businesses expand into new regions, especially fast-growing ones like India, they must understand and adapt to regional compliance mandates or risk falling behind.
India’s regulatory environment demands attention. It blends global expectations with local rules designed to protect digital sovereignty, user data, and national interests. Whether you’re processing payments, handling personal data, or operating in sectors like finance, telecom, or healthcare, Indian laws expect companies to follow strict, evolving standards.
In this article, we’ll explore India’s most important regulatory compliance mandates, including the Digital Personal Data Protection Act (DPDPA) and key guidelines from the RBI, SEBI, and other regulators. You’ll also learn how to manage compliance more efficiently using modern tools like regulatory compliance software, and how smart planning can help your business grow without hitting legal roadblocks.
Understanding India’s Regulatory Compliance Landscape
India’s regulatory environment has evolved rapidly in response to digital transformation, cybersecurity risks, and the need to protect consumer rights. Today, businesses across industries must navigate a mix of sector-specific regulations, national data protection laws, and financial governance standards. Failing to comply doesn’t just result in fines—it can halt operations, damage reputations, or even lead to shutdowns.
But before we dive into each regulatory compliance framework, let’s first understand what regulatory compliance means?
Regulatory Compliance Meaning: What It Really Involves
At its core, regulatory compliance means following the laws, standards, and policies that apply to your business. These rules could come from government agencies, industry bodies, or international regulators. They exist to protect consumers, ensure fair competition, and maintain security—especially in sensitive areas like finance, healthcare, and data privacy.
But regulatory compliance meaning goes beyond just knowing the rules. It involves:
- Identifying applicable laws: You must know which regulations apply to your business based on your industry, location, and operations.
- Building internal controls: You need documented policies, secure systems, and responsible workflows to meet those legal standards.
- Monitoring and reporting: Most regulations require you to regularly prove compliance through audits, reports, or third-party attestations.
India doesn’t rely on a single framework. Instead, it uses a multi-layered compliance model. Various regulators oversee different industries and enforce their own rules. Here’s how that plays out:
1. Digital Personal Data Protection Act (DPDPA), 2023
India’s DPDPA gives individuals control over their personal data and holds businesses accountable for how they collect, use, and store it. It requires data localization, meaning you must store certain types of personal data within India. Whether you’re an Indian startup or a global tech firm, if you process data related to Indian users, this law applies to you.
Key Requirements:
1. Lawful Processing of Personal Data
Organizations (referred to as Data Fiduciaries) must:
- Collect and process only necessary data for a clear and lawful purpose.
- Inform individuals (Data Principals) at the time of collection about how their data will be used, stored, and shared.
- Obtain explicit consent in clear, plain language—no pre-checked boxes or legal jargon.
2. Consent and Notice Requirements
- Consent must be free, informed, specific, and unambiguous.
- Notices must clearly explain:
- Purpose of processing
- Nature of personal data collected
- Rights available to individuals
- Purpose of processing
- Individuals must have the option to withdraw consent at any time.
3. Data Principal Rights
The DPDPA grants several rights to individuals, including:
- Right to access personal data being processed
- Right to correction and erasure of inaccurate or outdated data
- Right to grievance redressal through a designated channel
- Right to nominate someone to exercise rights on their behalf in case of death or incapacity
Organizations must provide mechanisms to address these rights within a reasonable time.
4. Obligations of Data Fiduciaries
Fiduciaries (i.e., organizations collecting data) must:
- Implement technical and organizational safeguards (e.g., encryption, access control)
- Limit data sharing and ensure third parties follow equivalent data protection standards
- Notify the Data Protection Board and affected individuals in case of a data breach
- Retain data only as long as necessary, and delete it when no longer required
5. Special Obligations for Significant Data Fiduciaries
The government may classify certain organizations as Significant Data Fiduciaries (SDFs) based on:
- Volume and sensitivity of data processed
- Potential impact on national interest or public order
SDFs must:
- Appoint a Data Protection Officer (DPO)
- Conduct Data Protection Impact Assessments (DPIAs)
- Undergo periodic audits and compliance checks
6. Data Localization Not Mandatory (But Encouraged)
Unlike earlier drafts, the final version of the DPDPA does not mandate complete data localization. However, it empowers the government to restrict data transfers to certain countries if deemed necessary for national security or public interest.
7. Grievance Redressal and Regulatory Oversight
- Organizations must establish grievance redressal mechanisms for individuals to raise data-related complaints.
- The proposed Data Protection Board of India will investigate violations and impose penalties.
8. Penalties for Non-Compliance
Penalties under DPDPA are significant:
- Up to ₹250 crore (~USD 30 million) for failure to prevent data breaches
- Fines for non-compliance with consent, data rights, and breach notification requirements
- Monetary penalties vary based on severity and nature of the violation
2. Reserve Bank of India (RBI) Cybersecurity Framework
Regulator: RBI (applies to banks, NBFCs, and digital payment entities)
RBI has issued detailed cybersecurity guidelines for regulated entities to strengthen digital banking safety and reduce fraud.
Key Requirements:
- Establish a Cybersecurity Policy approved by the board
- Set up a Security Operations Center (SOC) for real-time threat monitoring
- Conduct risk assessments, penetration testing, and vulnerability scanning
- Report major incidents to RBI within prescribed timeframes
- Maintain business continuity and disaster recovery plans
For Payment Aggregators:
RBI also mandates tokenization, encryption, and data storage rules, particularly around cardholder data.
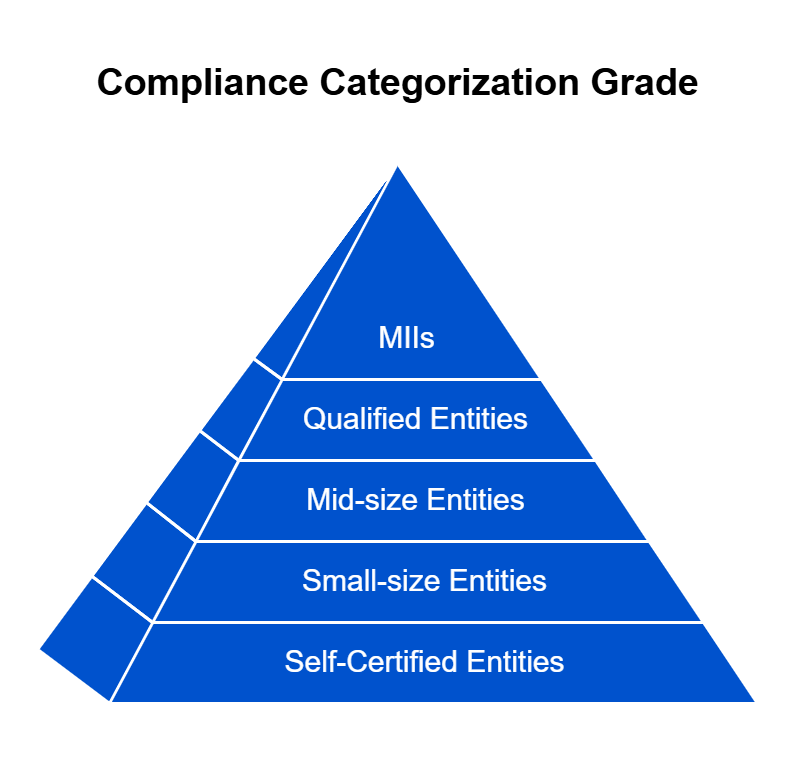
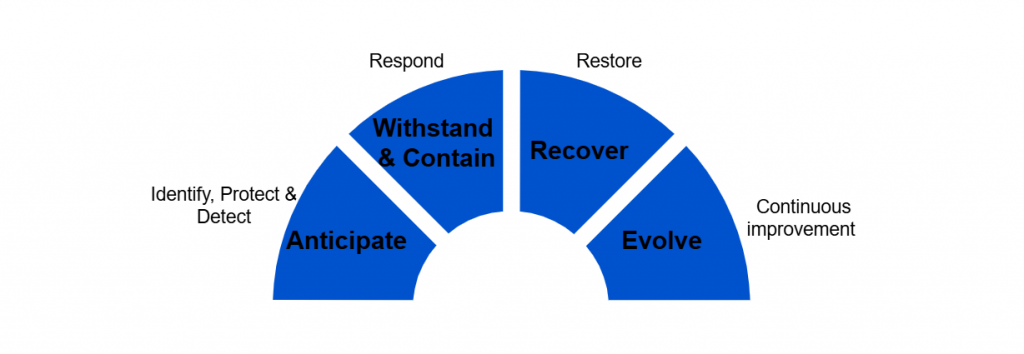
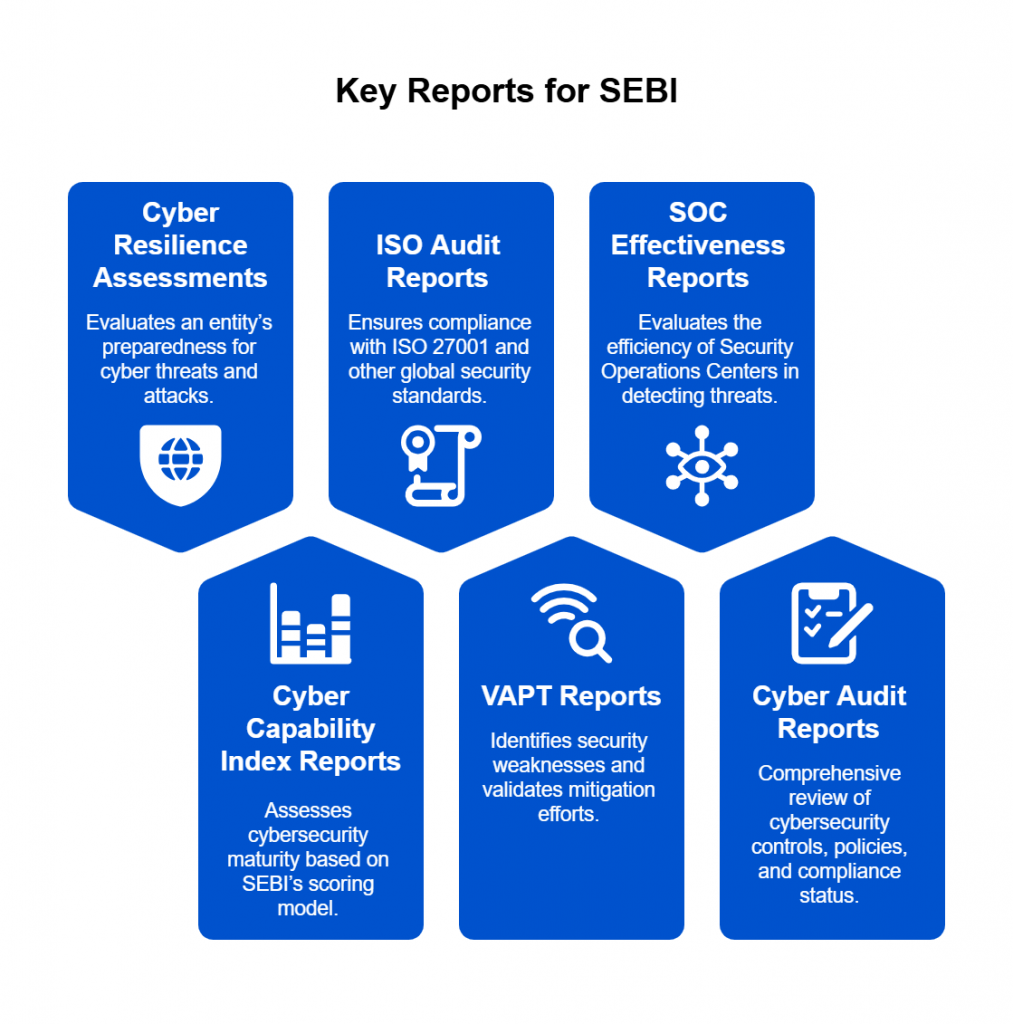
3. SEBI Cybersecurity and Cyber Resilience Framework
For companies in financial markets, SEBI ensures data integrity, system security, and reporting accuracy. Listed companies must meet strict requirements around IT audits, insider trading prevention, and cybersecurity readiness.
Key Requirements:
- Establish a Cybersecurity and Resilience Policy
- Appoint a Chief Information Security Officer (CISO)
- Implement multi-layered access controls
- Monitor logs through SIEM systems
- Submit quarterly reports on security posture and incidents
4. CERT-In Guidelines (April 2022 Notification)
Regulator: Indian Computer Emergency Response Team (CERT-In), under the Ministry of Electronics and IT (MeitY)
CERT-In is India’s national nodal agency for responding to cybersecurity incidents. In April 2022, it issued sweeping guidelines to strengthen cybersecurity practices across all organizations offering digital services in India.
Key Compliance Requirements:
- Reporting cyber incidents (like data breaches, ransomware, or system compromise) within 6 hours
- Maintaining logs of all ICT systems for 180 days, stored within India
- Time synchronization with NTP servers for accuracy in forensic investigations
- Retention of user data by VPN providers, cloud service companies, and crypto exchanges for 5 years
- Appointing a point of contact (PoC) for coordination with CERT-In
Penalties for Non-Compliance:
Non-compliance can result in penalties under the IT Act, including fines and prosecution.
5. Information Technology (Reasonable Security Practices and Procedures) Rules, 2011
Regulator: Ministry of Electronics and Information Technology (MeitY)
Overview:
These rules form the backbone of India’s cybersecurity regulations. They define what qualifies as reasonable security practices, especially for companies handling sensitive personal data or information (SPDI).
Key Compliance Requirements:
- Implement an IS/ISO/IEC 27001-based Information Security Management System (ISMS)
- Develop a detailed privacy policy
- Conduct periodic audits to validate security practices
- Obtain user consent for data collection and processing
Sector Relevance:
Applies broadly across industries, especially those managing large volumes of personal data.
6. IRDAI Cybersecurity Regulations for Insurers
The Insurance Regulatory and Development Authority of India (IRDAI) mandates insurers to adopt strong cybersecurity practices to protect policyholder data and ensure operational resilience.
Board-Approved Cybersecurity Policy
- Align with international standards (e.g., ISO 27001, NIST)
- Review annually or after major incidents
Appointment of Chief Information Security Officer (CISO)
- CISO oversees cybersecurity governance and reports to senior management
Risk-Based Cybersecurity Framework
- Conduct regular risk assessments and vulnerability scans
- Extend controls to third-party vendors
24×7 Security Operations and Monitoring
- Implement a Security Operations Center (SOC)
- Retain system logs for a minimum of 180 days
Incident Reporting to IRDAI
- Report significant cyber incidents within 24 hours
- Submit root cause analysis and remedial action plan
Business Continuity and Disaster Recovery (BCP/DR)
- Develop and test plans regularly to ensure service availability
Data Protection and Privacy
- Encrypt sensitive data in transit and at rest
- Enforce role-based access control and data classification
Cybersecurity Awareness Training
- Conduct periodic training for employees and relevant third parties
Audit and Compliance Reporting
- Perform regular internal and third-party security audits
- Submit annual cybersecurity compliance certificate to IRDAI
6. Industry-Specific Mandates
- Healthcare providers must protect patient data under the Clinical Establishments Act and follow ethical standards, some of which align with international regulations like HIPAA.
- E-commerce platforms must follow the Consumer Protection (E-commerce) Rules, 2020, which focus on fair practices, data handling, and customer redressal.
- Digital media and EdTech companies often face compliance checks from MeitY and other ministries to ensure safe content and responsible data usage.
As you can see, regulatory compliance in India isn’t one-size-fits-all. That’s why businesses need a structured regulatory compliance management strategy to stay ahead of evolving laws, reduce operational risk, ensure audit readiness, and build long-term trust with customers, partners, and regulators.
Unifying Compliance Strategies Across India’s Regulatory Mandates
India’s compliance landscape can feel overwhelming. Each regulator—from the RBI and SEBI to TRAI and MeitY—has its own set of rules. These laws often overlap, evolve quickly, and require different types of documentation, audits, and reporting timelines. Managing them in silos doesn’t just create extra work—it increases the risk of something slipping through the cracks.
That’s why businesses need a unified compliance strategy—one that brings all requirements under a common framework, supported by clear processes and the right technology.
1. Start With a Central Compliance Inventory
Create a master list of all regulatory mandates that apply to your organization. Include:
- The regulation name and governing body
- The specific requirements (e.g., data localization, access control, reporting frequency)
- Associated business processes or systems
- Key compliance owners or teams
This inventory acts as your single source of truth, helping you spot overlap and gaps.
2. Map Overlapping Controls
Many Indian regulations share common goals—like protecting customer data or ensuring financial integrity. For example:
- RBI and DPDPA both emphasize data security and privacy
- SEBI and RBI both require IT audits and risk assessments
- TRAI and MeitY both touch on user consent and data governance
By mapping overlapping controls across mandates, you can reduce duplication. One well-designed process can often fulfill multiple requirements.
3. Standardize Policies and Documentation
Draft compliance policies that cover shared requirements across frameworks. Instead of creating separate documents for each regulator, use common templates and clearly indicate where each policy meets specific laws. This makes reviews and audits smoother and easier to manage.
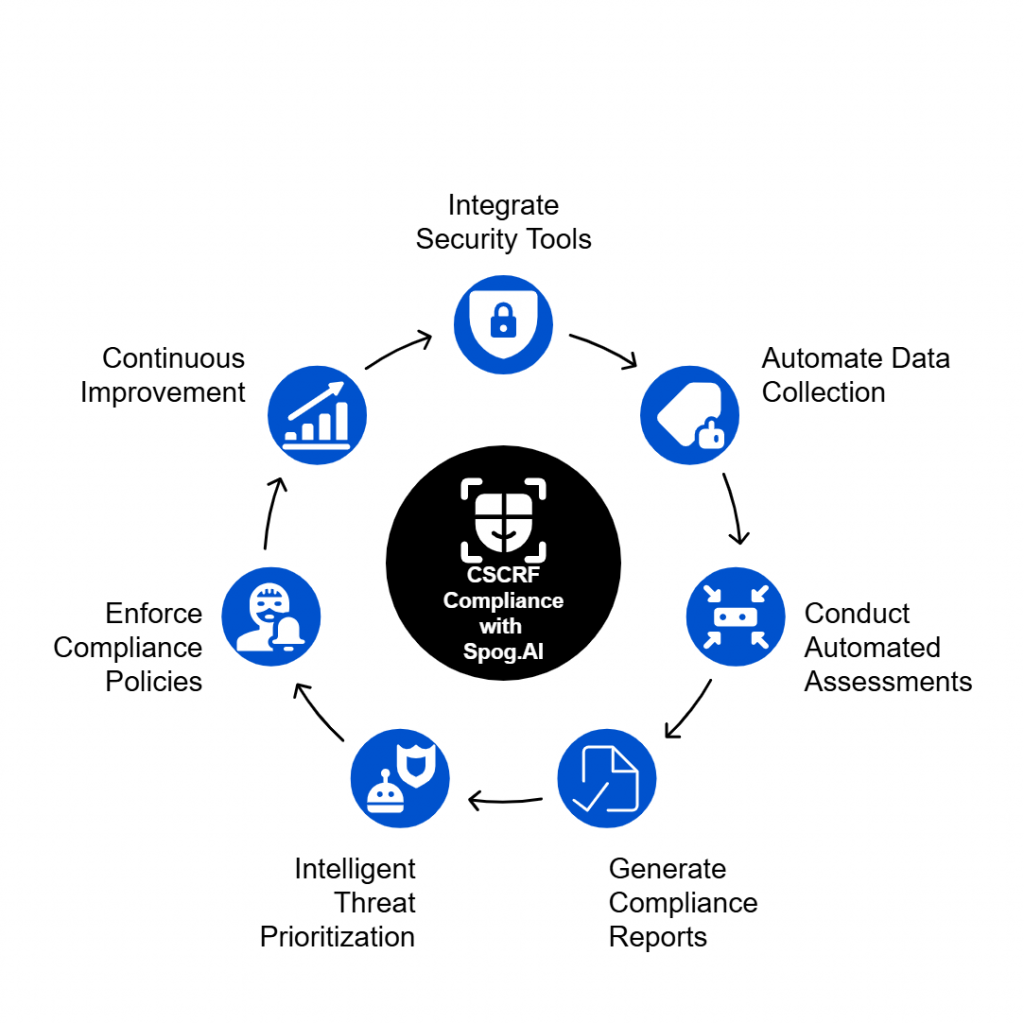
4. Automate Monitoring and Evidence Collection
Use regulatory compliance software such as Spog.AI to track key metrics, generate audit logs, and gather proof of compliance. Automation helps you:
- Stay updated on changing laws
- Reduce manual effort
- Generate consistent audit trails
Tools can also send alerts when a control fails or when it’s time to update a document—helping you stay proactive, not reactive.
5. Align Audit Timelines and Stakeholders
Rather than preparing for multiple audits at different times, align your internal reviews and external certifications. A coordinated calendar allows teams to prepare once and use the same evidence across multiple mandates.
Also, assign compliance champions in each business unit. These are people who understand both the operations and the regulations, acting as bridges between legal, IT, and leadership.
A unified strategy not only keeps you compliant—it helps your business run more efficiently. It turns compliance from a reactive task into a built-in strength, supporting your growth while reducing legal and reputational risks.
Steps to Implement Regulatory Compliance in Your Organization
Implementing regulatory compliance may seem daunting at first—but with a structured plan, you can turn it into a manageable, repeatable process. Whether you’re navigating India’s data protection laws, financial regulations, or industry-specific rules, the following steps will help you build a solid compliance foundation and stay ahead of risks.
1. Identify Applicable Regulations
Start by determining which laws and standards apply to your business. This depends on:
- Your industry (e.g., finance, healthcare, telecom)
- Your business model (e.g., e-commerce, SaaS, manufacturing)
- The type of data you collect and store (e.g., personal, financial, health-related)
For example, if you process payments, you’ll need to follow RBI guidelines. If you handle user data, the Digital Personal Data Protection Act (DPDPA) applies.
2. Conduct a Compliance Gap Assessment
Once you’ve identified the relevant mandates, assess your current processes. Ask:
- Where are we already compliant?
- What areas need improvement?
- Which controls are missing altogether?
A gap assessment helps you understand your starting point and build a roadmap to full compliance.
3. Build a Regulatory Compliance Framework
Create internal policies, procedures, and controls that align with the requirements. This framework should include:
- A compliance policy outlining responsibilities and expectations
- Risk management practices
- Incident response procedures
- Regular audit and review schedules
Document everything clearly, as you’ll need it for audits and reporting.
4. Assign Ownership and Form a Compliance Team
Compliance isn’t one person’s job. Assign clear roles:
- Legal or risk managers to interpret regulations
- IT/security teams to implement technical controls
- HR and operations to support training and internal policies
Form a cross-functional compliance committee to drive accountability and ensure collaboration.
5. Train Employees Across Departments
Educate your team on what compliance means for their specific roles. For example:
- Customer service teams should know how to handle user data securely
- Developers should follow secure coding practices
- Finance teams should understand audit and reporting obligations
Regular, role-specific training builds a compliance-aware culture.
6. Leverage Regulatory Compliance Software
Automate repetitive tasks like:
- Monitoring control status
- Collecting audit evidence
- Tracking regulatory updates
- Generating compliance reports
These tools streamline your efforts, reduce errors, and help you stay proactive—especially in complex environments like India.
7. Monitor, Audit, and Improve Continuously
Compliance isn’t a one-time project. Set up recurring internal audits and self-assessments. Monitor changes in laws and adjust your framework accordingly. Use findings from audits to close gaps, update policies, and improve controls.
Staying compliant means staying dynamic—especially when regulations evolve as quickly as they do in India.
Transform Compliance Into a Strategic Advantage
India’s regulatory environment challenges businesses—but also offers them an opportunity. When companies treat compliance as a strategic priority, not just a legal burden, they gain more than just certification—they build trust, improve systems, and boost resilience.
Regulators like the RBI, SEBI, IRDAI, and CERT-In, along with the Digital Personal Data Protection Act (DPDPA), lay down clear expectations. Businesses that identify their obligations early, streamline overlapping mandates, and adopt smart compliance tools can reduce risk and stay audit-ready year-round.
By training teams, automating processes, and integrating compliance into day-to-day operations, organizations don’t just stay out of trouble—they stay ahead. Companies that build a culture of accountability and transparency position themselves to scale faster, enter new markets, and strengthen customer loyalty.
Use compliance as a lever, not a hurdle. When you embed it into your strategy, you do more than meet legal standards—you create long-term value.