The problem isn’t that companies ignore risk—it’s that they look for it in the wrong places. Traditional risk analysis focuses almost entirely on technology, scanning for vulnerabilities in firewalls, networks, and databases. While these are critical areas, this method overlooks the bigger picture: risk doesn’t just live in IT infrastructure—it exists in human behavior, business operations, and everyday decisions.
Consider this: a well-secured system means little if employees fall for phishing scams, vendors mishandle sensitive data, or outdated policies create loopholes for attackers. According to estimates from Statista’s Market Insights, the global cost of cybercrime is anticipated to surge dramatically, escalating from $9.22 trillion in 2024 to a staggering $13.82 trillion by 2028. Yet, many of these breaches stem from process failures and human error rather than just technical vulnerabilities.
A holistic risk audit shifts the focus. Instead of treating security as an IT issue, it treats risk as a business problem—analyzing how people, processes, technology, and information intersect to create vulnerabilities. This method moves beyond static compliance checklists and integrates stakeholder insights, business-critical workflows, and real-world risk scenarios into the assessment. It’s not just about securing infrastructure—it’s about securing how business gets done.
In this article, we’ll explore how to conduct a holistic risk audit that actually strengthens security, builds resilience, and promotes a security-first culture across the organization. Because in today’s world, risk isn’t just an IT concern—it’s everyone’s responsibility.
The Limitations of Traditional Risk Analysis and the Need for Comprehensive Risk Approach
Most organizations conduct risk assessments with a technology-first mindset, focusing heavily on technical vulnerabilities while overlooking physical and administrative risks. While cybersecurity tools, penetration testing, and network scans are important, they paint an incomplete picture of an organization’s true risk exposure.
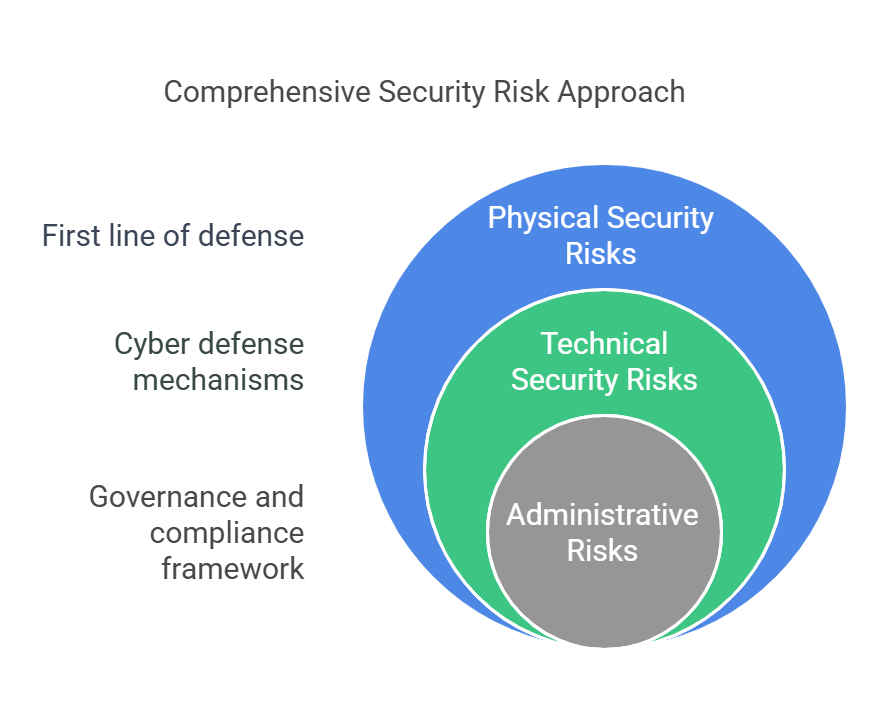
A comprehensive risk approach requires evaluating three key areas: physical, technical, and administrative controls.
1. Physical Security Risks: Protecting the First Line of Defense
Physical security is often overlooked in risk assessments, yet it forms the first layer of defense against unauthorized access, theft, and environmental hazards. A strong digital security framework means little if bad actors can gain physical access to sensitive systems or data centers.
Key aspects of physical security controls include:
- Access Control Systems – Badge entry, biometric authentication, and visitor management to prevent unauthorized access.
- Surveillance & Monitoring – CCTV cameras, security personnel, and alarm systems to deter and detect security threats.
- Environmental Safeguards – Fire suppression systems, backup power solutions, and disaster recovery planning to protect infrastructure from natural disasters or power failures.
- Device Security – Locking down servers, workstations, and storage devices to prevent hardware theft or tampering.
Without proper physical controls, cyber risks increase. For example, an attacker bypassing network security measures by plugging in a rogue USB device or gaining unauthorized access to a server room poses a serious risk to an organization’s security.
2. Technical Security Risks: Strengthening Cyber Defenses
Technical controls are at the core of cybersecurity, protecting systems from external attacks, internal threats, and data breaches. Organizations typically focus on firewalls, intrusion detection, and encryption, but a truly effective technical risk assessment goes beyond just identifying vulnerabilities—it evaluates how security measures integrate with business operations and user behavior.
Key technical controls include:
- Identity & Access Management (IAM) – Role-based access control (RBAC), multi-factor authentication (MFA), and privileged access management (PAM) to prevent unauthorized system access.
- Network Security – Firewalls, intrusion prevention systems (IPS), and endpoint detection to monitor and defend against cyber threats.
- Data Protection – Encryption, secure backups, and data loss prevention (DLP) to safeguard sensitive information.
- Vulnerability & Patch Management – Regular system updates, vulnerability scans, and automated patching to minimize security gaps.
Many organizations struggle with keeping up with emerging cyber threats, leading to outdated security configurations and unpatched software vulnerabilities. A holistic risk audit ensures that security controls are not only in place but also consistently monitored, updated, and aligned with evolving threats.
3. Administrative Risks: Strengthening Policies, Compliance & Awareness
Even with strong physical and technical controls, security risks remain high if policies, procedures, and employee behavior are not properly managed. Administrative controls provide the governance framework that ensures security policies are followed and compliance requirements are met.
Key administrative controls include:
- Security Policies & Procedures – Clearly defined access controls, incident response plans, and acceptable use policies that guide security practices.
- Employee Training & Awareness – Regular security awareness training to prevent phishing attacks, social engineering, and insider threats.
- Regulatory Compliance & Audits – Ensuring adherence to SOC 2, ISO 27001, GDPR, HIPAA, and other industry standards through periodic audits.
- Third-Party & Vendor Risk Management – Evaluating security measures in place for external vendors, contractors, and business partners who may have access to sensitive data.
A major administrative risk is the lack of involvement from business users in security planning. Traditional IT-centric risk assessments fail to engage key stakeholders, leading to policy gaps and misaligned security priorities. A holistic risk audit brings together IT teams, executives, compliance officers, and department leaders to ensure security policies are both effective and practical for real-world business operations.
Each of these three areas—physical, technical, and administrative controls—plays a crucial role in an organization’s overall security posture. Focusing on only one or two leaves gaps that attackers can exploit. A holistic risk audit addresses all three dimensions, ensuring that security is comprehensive, proactive, and aligned with business needs.
Developing a Risk Register and Scoring Methodology
Once an organization has identified risks across physical, technical, and administrative controls, the next step is to document, categorize, and prioritize these risks in a structured manner. This is where a risk register becomes essential.
A risk register is a centralized document that helps organizations track, assess, and manage risks. It provides a clear, standardized view of potential threats, their impact, and the necessary actions to mitigate them. Without a structured approach, risk management can become reactive, leading to missed vulnerabilities and inefficient resource allocation.
Building an Effective Risk Register
A well-designed risk register includes the following key components:
- Risk Description – A clear explanation of the risk, including where it originates and the potential impact.
- Likelihood – An assessment of how probable the risk is, based on past data and expert evaluation.
- Impact – The potential consequences if the risk materializes, such as financial loss, operational downtime, or reputational damage.
- Risk Score – A calculated value that combines likelihood and impact, helping to prioritize risks.
- Existing Controls – The security measures already in place to mitigate the risk.
- Mitigation Plan – Recommended actions to further reduce risk exposure.
- Risk Owner – The individual or team responsible for monitoring and addressing the risk.
Scoring Methodology: Quantifying Risk for Better Decision-Making
To effectively prioritize risks, organizations use a risk scoring methodology. This typically involves assigning numerical values to likelihood and impact, then multiplying them to generate a risk score.
For example, a 5×5 risk matrix categorizes risks as follows:
| Risk Level | Likelihood | Impact | Risk Score (L × I) | Priority |
| High | 5 (Very Likely) | 5 (Severe) | 25 | Critical |
| Medium-High | 4 (Likely) | 4 (High) | 16 | High |
| Medium | 3 (Possible) | 3 (Moderate) | 9 | Moderate |
| Low | 2 (Unlikely) | 2 (Low) | 4 | Low |
| Very Low | 1 (Rare) | 1 (Minimal) | 1 | Minimal |
A critical risk (25) requires immediate action, while a low-risk (4 or below) may only need periodic monitoring. This structured approach helps organizations prioritize resources efficiently—focusing on the most pressing security threats first.
Example Risk Register Entry
| Risk | Likelihood | Impact | Risk Score | Existing Controls | Mitigation Plan | Risk Owner |
| Unpatched critical vulnerability in ERP system | 5 (Very Likely) | 5 (Severe) | 25 | Monthly patching schedule | Implement automated patch management | IT Security Team |
| Unauthorized access to server room | 4 (Likely) | 4 (High) | 16 | Keycard access, security cameras | Implement biometric authentication | Facilities Manager |
| Lack of employee security awareness training | 3 (Possible) | 3 (Moderate) | 9 | Annual training | Move to quarterly training, add phishing simulations | HR & Compliance |
By consistently maintaining and updating a risk register, organizations can track risks over time, measure the effectiveness of security controls, and make data-driven decisions about risk mitigation.
The Value of a Risk Register in Holistic Risk Audits
A holistic risk audit relies on a risk register to bridge the gap between risk identification and action. It ensures that security threats across physical, technical, and administrative domains are:
- Documented and tracked over time
- Quantified using a structured methodology
- Assigned to responsible teams for resolution
- Regularly reviewed and updated to reflect new threats
The Role of Stakeholder Interviews and Evidence Collection
A risk audit is only as strong as the information that feeds it. While technical scans and automated tools provide valuable data, they cannot capture the full scope of risks that stem from business operations, human behavior, and process inefficiencies. This is why stakeholder interviews and evidence collection are critical in conducting a holistic risk audit.
Why Stakeholder Interviews Matter
Stakeholders—ranging from IT and security teams to compliance officers, department heads, and frontline employees—have firsthand knowledge of daily operations and potential security gaps that automated tools might overlook. Engaging them ensures that risk assessments reflect real-world challenges rather than just theoretical vulnerabilities.
Stakeholder interviews help to:
- Identify process-based risks that may not be evident through technical analysis, such as gaps in vendor security, inefficient access controls, or outdated employee onboarding procedures.
- Validate technical risks by understanding how employees interact with systems and whether security policies are being followed in practice.
- Uncover insider threats and social engineering risks, which are difficult to detect using automated tools alone.
- Align risk management efforts with business priorities, ensuring that mitigation strategies are practical and don’t disrupt critical workflows.
A structured interview process ensures consistency in gathering insights across departments. Questions should cover key areas such as security practices, compliance challenges, operational bottlenecks, and risk awareness among employees.
For example, while IT teams may flag unpatched software vulnerabilities as a major risk, interviews with department managers might reveal that employees routinely bypass security protocols to meet tight deadlines—introducing a new, unaccounted-for risk. These insights help organizations prioritize risk management strategies based on real-world behavior, not just system alerts.
The Importance of Evidence Collection
Beyond interviews, collecting concrete evidence ensures that risk assessments are based on verifiable data. Evidence collection involves gathering documentation, security logs, access records, and audit trails to validate the risks identified during interviews and technical assessments.
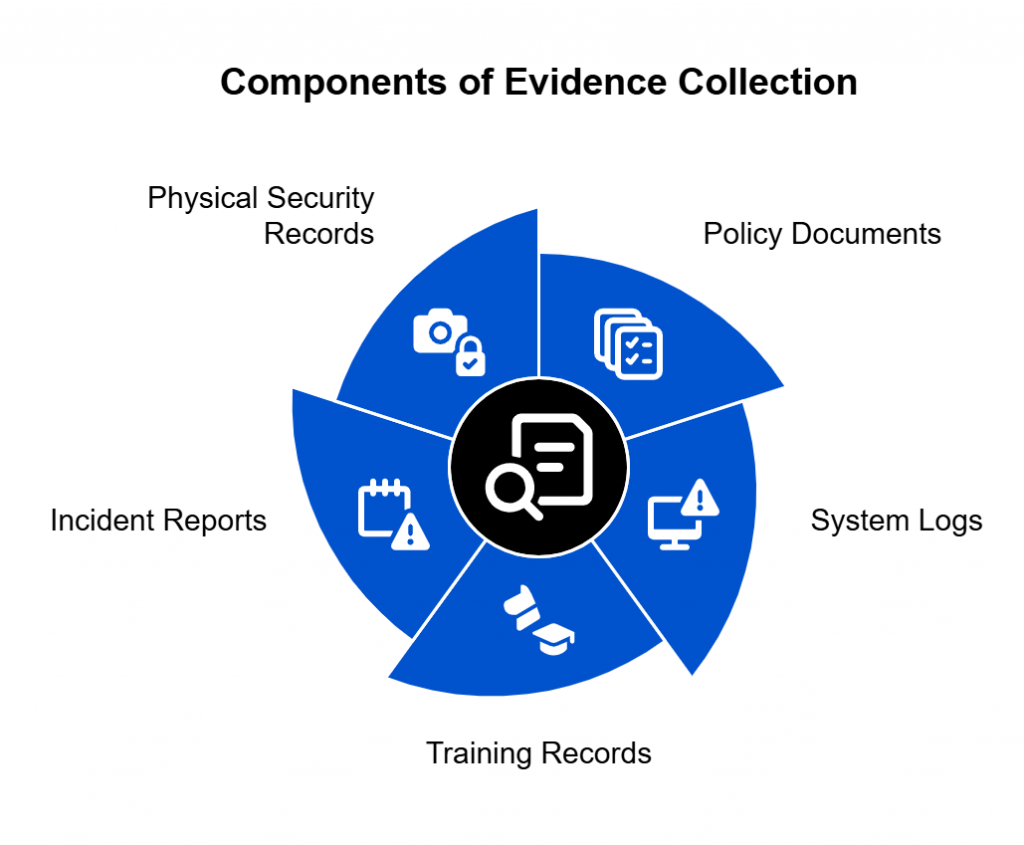
Key types of evidence include:
- Policy and procedural documents – To verify whether security policies align with best practices and compliance standards.
- System logs and audit trails – To detect unauthorized access, failed login attempts, and potential security incidents.
- Employee training records – To assess security awareness levels and identify gaps in training programs.
- Incident reports and past security breaches – To analyze trends in security failures and determine recurring risks.
- Physical security records – To evaluate access logs, video surveillance, and facility security measures.
Integrating Stakeholder Insights with Evidence-Based Risk Analysis
Combining stakeholder input with concrete evidence creates a well-rounded, accurate picture of an organization’s risk posture. It also helps in validating the findings from automated risk assessments and technical audits, ensuring that risk scoring is based on actual business operations, not just system-generated data.
For example, if IT security logs indicate multiple failed login attempts, but HR records show that departing employees haven’t had their credentials revoked, this highlights a procedural weakness in offboarding security protocols. Stakeholder interviews can then help clarify whether the issue stems from a lack of training, oversight, or policy enforcement—allowing organizations to take targeted corrective action.
By combining human insights with verifiable data, organizations can ensure that their risk audits are comprehensive, actionable, and aligned with both security and business goals.
Reporting Risk Audit Findings for Executive Buy-In
Conducting a holistic risk audit is only half the battle. To drive meaningful change, organizations must effectively communicate audit findings to executives and decision-makers in a way that resonates with business priorities. Simply presenting raw data or technical vulnerabilities isn’t enough—leaders need a clear, actionable report that ties risk to financial, operational, and reputational impact.
Tailoring the Report for Executives
Executives are responsible for strategic decision-making, risk management, and regulatory compliance, but they may not have deep technical expertise. An effective risk report should:
- Speak the language of business – Focus on risk in terms of financial loss, operational disruption, legal liability, and brand reputation.
- Highlight high-priority risks – Avoid overwhelming leadership with too much detail. Instead, summarize the most critical risks that require immediate action.
- Provide data-driven insights – Use risk scores, incident trends, and industry benchmarks to quantify risk levels.
- Recommend clear actions – Outline practical mitigation steps, including required resources, timelines, and cost estimates.
A well-structured report ensures that executives don’t just understand what the risks are but also why they matter and how to address them efficiently.
Structuring the Risk Audit Report
An executive-friendly risk report should follow a logical structure, ensuring that key points are easy to digest. Here’s an ideal format:
1️⃣ Executive Summary – A high-level overview of key findings, major risks, and overall security posture. This should be concise—one page at most.
2️⃣ Key Risk Areas – A breakdown of the top risks across physical, technical, and administrative domains, categorized by severity. Use a risk heatmap or visual indicators to highlight critical threats.
3️⃣ Financial & Business Impact – An explanation of how these risks could affect the bottom line, operational efficiency, legal standing, or customer trust. If possible, include estimated costs of potential breaches, downtime, or regulatory penalties.
4️⃣ Current Mitigation Efforts & Gaps – A comparison between existing controls and unaddressed vulnerabilities, providing a reality check on security readiness.
5️⃣ Recommended Actions – A clear action plan with short-term and long-term steps to reduce risk exposure. Include required resources, estimated costs, and responsible stakeholders for each mitigation effort.
6️⃣ Conclusion & Call to Action – A summary reinforcing the need for action, along with next steps such as allocating a budget, implementing new controls, or scheduling follow-up assessments.
Using Visuals to Make the Report More Impactful
Executives process information more effectively through visuals than dense reports. Incorporating the following can enhance clarity and engagement:
- Risk Heatmaps – A color-coded risk matrix to show the likelihood and impact of different threats at a glance.
- Financial Impact Graphs – Data-driven projections illustrating the potential costs of unaddressed risks versus mitigation investments.
- Trend Analysis Charts – Show patterns in risk incidents over time to highlight improvement areas or emerging threats.
- Comparative Benchmarks – Insights on how the organization’s risk posture compares to industry standards and regulatory expectations.
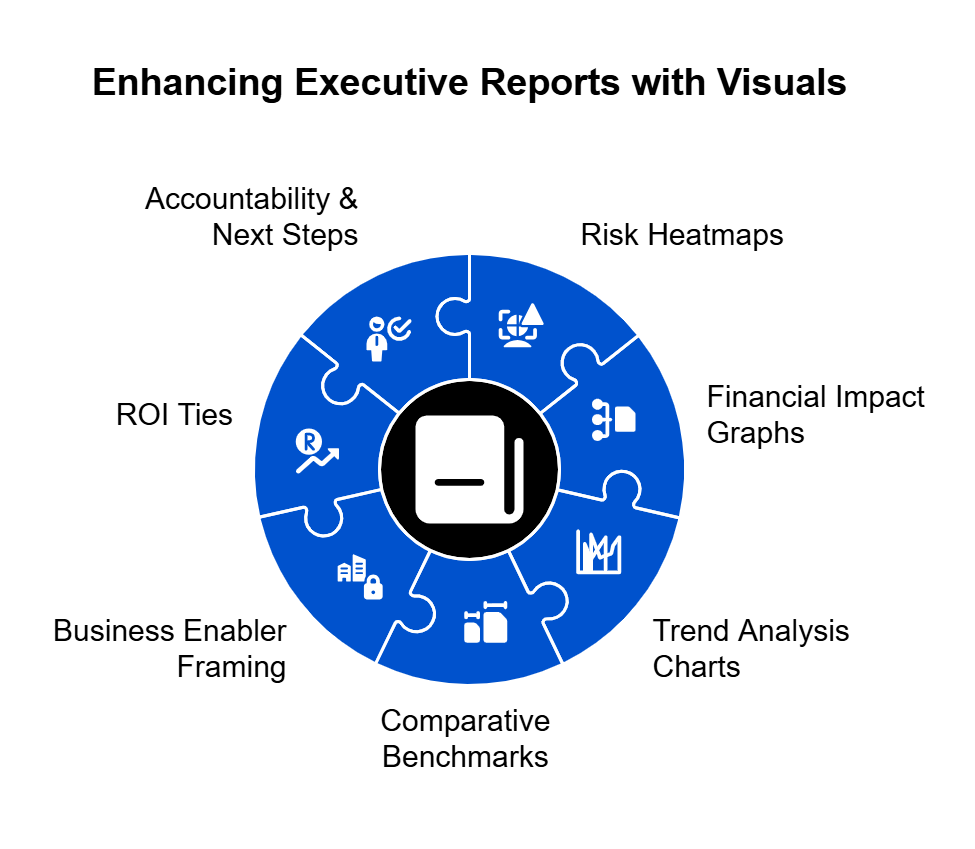
Driving Executive Buy-In for Risk Mitigation
Even with a strong report, securing executive buy-in requires a strategic approach. To persuade leadership to take action, risk managers should:
- Frame security as a business enabler – Show how improved risk management supports revenue growth, regulatory compliance, and competitive advantage, rather than being just a cost center.
- Tie recommendations to ROI – Demonstrate how investing in risk mitigation can prevent costlier security incidents, fines, or operational disruptions.
- Show accountability & next steps – Assign ownership to key stakeholders and present a timeline for implementing recommended actions.
By effectively communicating risk in business terms and providing clear, actionable insights, organizations can move risk management from a reactive, compliance-driven function to a proactive, strategic initiative.
Making Risk Audits a Continuous Process
Risk management is not a one-time task. It needs to adapt to evolving threats, regulatory changes, and business growth. However, many organizations struggle to keep their risk registers updated, engage stakeholders effectively, collect necessary evidence, and generate meaningful reports. Manual processes can be time-consuming, prone to human error, and difficult to scale.
Automation helps organizations streamline risk audits, ensuring risks are continuously identified, assessed, and managed without overwhelming security teams.
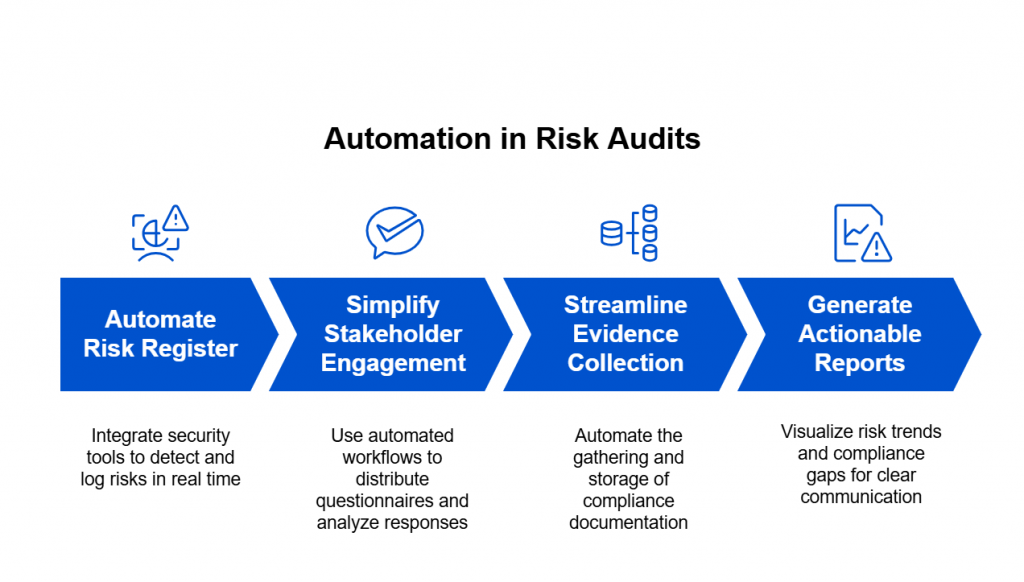
How Automation Enhances Risk Audits
1️⃣ Automating the Risk Register
Keeping a risk register up to date requires constant tracking and prioritization. Automation helps by integrating with security tools to detect, score, and log risks in real time, reducing manual data entry and improving accuracy.
2️⃣ Simplifying Stakeholder Engagement
Traditional risk interviews and assessments often involve scheduling conflicts, lost emails, and inconsistent responses. Automated workflows can distribute structured questionnaires, track responses, and analyze insights efficiently, ensuring all relevant perspectives are captured.
3️⃣ Streamlining Evidence Collection
Gathering compliance documentation, security logs, and audit trails manually can be a bottleneck. Automating evidence collection ensures that required data is consistently gathered and stored, reducing last-minute efforts before audits.
4️⃣ Generating Actionable Reports
Risk reports often need to be translated into clear business terms for executive teams. Automation can help by visualizing risk trends, financial impacts, and compliance gaps, making it easier to communicate findings and prioritize remediation.
Moving Toward Continuous Risk Management with Spog.AI
A holistic risk audit should not be a one-time event. By automating risk tracking, assessments, evidence collection, and reporting, organizations can shift from a reactive to a proactive approach—reducing security gaps, improving compliance readiness, and making risk management an ongoing process.
Spog.AI helps organizations streamline their risk audits by automating the entire lifecycle—from risk identification and stakeholder engagement to evidence collection and reporting. With real-time risk tracking, AI-driven analysis, and seamless compliance workflows, Spog.AI ensures security teams can focus on what matters most—mitigating risks and strengthening security posture.
To learn how Spog.AI can help optimize your risk management process, schedule a demo today.
