Introduction: Why Efficacy Matters in Risk Assessment Tools
Cyberattacks don’t wait — and your detection tools shouldn’t either.
As threats grow more advanced and frequent, security teams must act faster and smarter. Relying on outdated tools or periodic checks is no longer enough. Today, tools like Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) are critical for spotting and stopping threats — and for helping teams understand their true risk exposure.
These tools are gaining serious traction. Recent reports show that 58% of organizations have deployed or are implementing XDR, a clear sign that businesses are moving toward smarter, more connected security solutions. The global XDR market was valued at $754.8 million in 2022, and it’s expected to grow at 20.7% annually through 2030.

Why the shift? Because they deliver. Security teams using integrated tools like SIEM and XDR report a 93% improvement in threat detection. And third-party tests confirm that solutions like XDR are effective at identifying and stopping advanced threats.
In this article, we’ll explore the move from EDR to XDR, how these tools support better risk assessments, and how to measure whether your tools are doing the job they promise.
Understanding EDR vs. XDR: Coverage, Pros & Cons
Choosing the right detection tool starts with understanding what each one does — and where it shines.
What is EDR?
Endpoint Detection and Response (EDR) focuses on monitoring and protecting endpoints such as laptops, servers, and mobile devices. It provides deep visibility into endpoint activity, detects suspicious behavior, and enables incident response directly on the device.
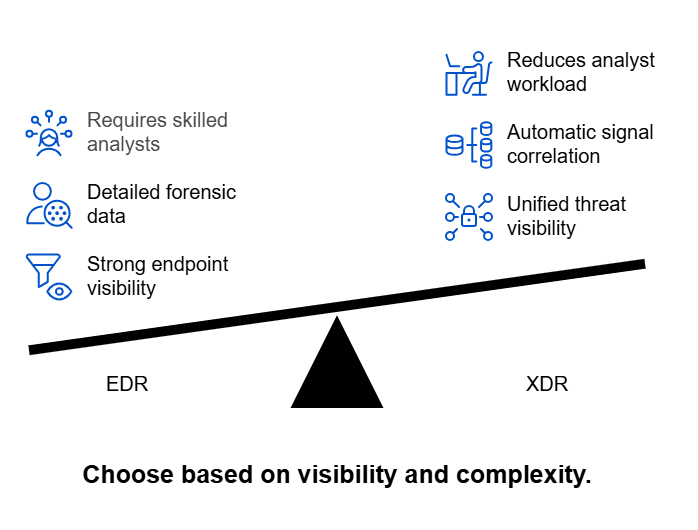
Pros:
- Strong visibility into individual endpoint behavior
- Detailed forensic data for investigations
- Effective for detecting malware, ransomware, and insider threats
Cons:
- Limited to endpoint data
- Can create alert fatigue without broader context
- Requires skilled analysts to investigate and correlate threats manually
What is XDR?
Extended Detection and Response (XDR) builds on EDR by combining data from multiple sources — endpoints, networks, cloud workloads, email, and more. The goal is to provide a unified view of threats across the entire IT environment, helping teams detect complex attacks faster and respond more efficiently.
Pros:
- Unified threat visibility across multiple layers (not just endpoints)
- Correlates signals automatically for faster detection
- Reduces analyst workload through context-rich alerts
Cons:
- Vendor capabilities vary significantly
- Can be more complex to implement, especially in hybrid environments
- May require integration with existing SIEM/SOAR tools for full value
EDR is focused and deep. XDR is broad and connected. While EDR excels at protecting endpoints, XDR helps teams understand the full scope of an attack — making it a powerful tool for organizations facing increasingly complex threats.
How Detection Tools Feed into Risk Scoring
Understanding the strengths and limitations of EDR and XDR is only part of the equation. The real value comes when these tools go beyond detection — and actively inform your risk assessments.
Modern security teams are shifting from alert-driven response to risk-driven strategy. This requires tools that don’t just spot threats, but also provide the context needed to evaluate their potential impact
From Alerts to Actionable Risk Insights
Detection tools generate a constant stream of telemetry — from endpoint anomalies to cloud-based threats. When this data is analyzed in isolation, it creates noise. But when it’s correlated and contextualized, it becomes a powerful input for dynamic risk scoring.
This central system aggregates alerts, behavior signals, and contextual information from across your environment to calculate real-time risk scores.
These scores help security teams move from alert fatigue to informed decision-making — prioritizing what matters based on business impact, exposure, and urgency.
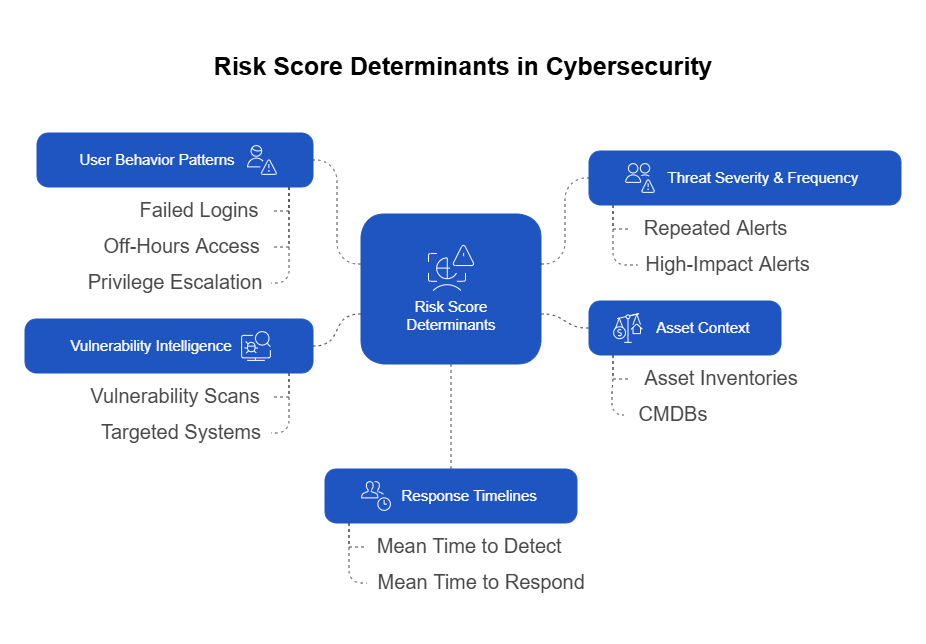
Key Data Inputs from EDR/XDR That Shape Risk Scores:
- Threat Severity & Frequency
Repeated or high-impact alerts raise the risk level of systems or users, especially when seen across different environments. - Asset Context
Integrating detection data with asset inventories or CMDBs allows systems to weigh risk based on asset value or criticality. - User Behavior Patterns
Actions like failed logins, off-hours access, or privilege escalation can increase a user’s individual risk score dynamically. - Vulnerability Intelligence
Merging vulnerability scan data with detection activity surfaces which systems are not just vulnerable — but actively being targeted. - Response Timelines
Metrics like Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR) reveal how long threats dwell in the environment, influencing overall risk.
Tips for Selecting the Right Solution for Your Organization
Not all detection and response tools are built the same — and not every organization needs the most advanced, feature-rich platform on the market. Choosing the right solution depends on your organization’s size, complexity, existing infrastructure, and internal expertise.
Here are key factors to guide your selection process:
1. Align with Organizational Complexity
- Smaller organizations may benefit from streamlined tools with strong out-of-the-box capabilities and minimal setup overhead. Focus on simplicity and ease of deployment.
- Larger enterprises should consider platforms that support multi-domain data ingestion, high-volume alert handling, and advanced correlation across cloud, network, and endpoint environments.
2. Ensure Integration Compatibility
The tool should fit into your existing tech stack, not force you to rip and replace. Look for solutions that:
- Offer open APIs for integration
- Work seamlessly with your SIEM, SOAR, and ticketing systems
- Support native connectors for your cloud and identity platforms
3. Evaluate Analyst Experience & Resource Availability
- If your security team is lean, automation, guided investigation, and context-rich alerts become essential.
- If you have an experienced SOC, prioritize tools that offer customization, deep telemetry, and advanced threat hunting capabilities.
4. Prioritize Risk-Based Features
Choose tools that feed into a centralized risk engine and offer:
- Dynamic risk scoring
- Asset and user risk visibility
- Business context tagging
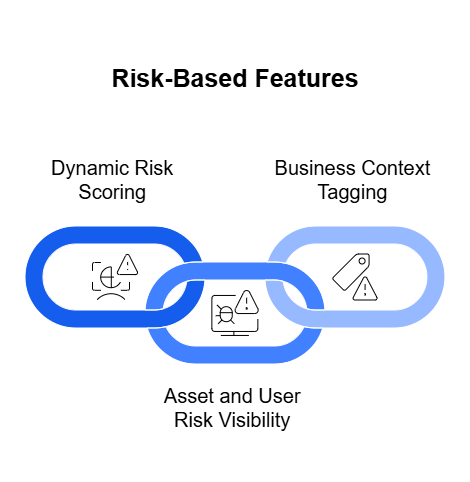
These capabilities ensure you’re not just detecting threats, but understanding their real-world impact.
5. Consider Scalability and Vendor Transparency
Your needs today might look very different in a year. Make sure the solution:
- Can scale with your environment
- Has transparent pricing and support models
- Provides clear product roadmaps and security certifications
Key Takeaway
The best detection solution isn’t necessarily the one with the most features — it’s the one that aligns with your goals, integrates into your ecosystem, and helps your team take smart, risk-informed action.
Metrics for Ongoing Tool Efficacy Evaluations
Choosing the right detection tool is just the beginning. To ensure it continues delivering value, security leaders need to measure its performance over time. This means going beyond vendor claims and looking at real-world impact across detection, response, and risk reduction.
Here are the key metrics that matter:
1. Mean Time to Detect (MTTD)
How quickly does the tool identify threats once they enter your environment?
A lower MTTD indicates faster threat recognition, which helps reduce potential damage.
2. Mean Time to Respond (MTTR)
How long does it take your team to contain or remediate an incident after detection?
A high MTTR can signal process bottlenecks or tool inefficiencies.
3. Detection Accuracy
Look at the balance between true positives, false positives, and false negatives.
Too many false alerts waste analyst time. Missed detections are even worse — they can lead to breaches.
4. Coverage and Visibility
Is the tool monitoring all critical areas — endpoints, cloud, network, identity, etc.?
Incomplete visibility limits your ability to assess and manage risk effectively.
5. Risk Score Alignment
Do the tool’s insights align with your organization’s risk priorities?
Check if dynamic risk scores reflect real-world business impact and evolving threat exposure.
6. Analyst Efficiency
How has the tool impacted your team’s productivity?
Track ticket resolution time, investigation depth, and the number of incidents handled per analyst.
7. Threat Intelligence Correlation
Is the tool incorporating external threat intelligence to enrich detection and response?
Effective solutions enhance internal data with global threat trends for smarter decisions.
| Metric | What It Measures | Why It Matters |
| Mean Time to Detect (MTTD) | Time taken to identify a threat after it enters the environment | Indicates how quickly threats are detected, helping minimize potential damage |
| Mean Time to Respond (MTTR) | Time taken to contain or remediate a threat after detection | Reflects how efficient your response processes and tools are |
| Detection Accuracy | Ratio of true positives to false positives and false negatives | High accuracy reduces alert fatigue and ensures threats aren’t missed |
| Coverage and Visibility | Scope of monitored assets (endpoints, cloud, network, identity, etc.) | Ensures comprehensive monitoring of your threat surface |
| False Positive Rate | Percentage of alerts that do not represent real threats | A high rate wastes analyst time and undermines trust in the tool |
| False Negative Rate | Percentage of real threats missed by the system | Missed detections increase exposure to breach and business disruption |
| Risk Score Accuracy | Alignment of risk scores with real-world threat and asset context | Helps prioritize remediation efforts based on business impact |
| Analyst Efficiency | Volume of alerts handled, time per investigation, resolution rate | Reflects how well the tool supports human analysts and workflows |
| Automated Response Rate | Percentage of threats mitigated through automated playbooks | Demonstrates the maturity and efficiency of response automation |
| Threat Intelligence Usage | Integration and application of external threat intelligence | Enhances detection and response with broader context and up-to-date threat data |
| Alert Correlation Rate | Ability to connect related alerts across systems and time | Reduces noise and improves incident clarity |
| Tool Uptime and Stability | Operational stability of the platform | Ensures consistent monitoring without service interruptions |
| Integration Depth | How well the tool integrates with other security platforms | Enables a more unified and effective security ecosystem |
Conclusion: From Detection to Strategic Risk Management
The security landscape has changed — and so must the way we evaluate our tools. It’s no longer enough for detection platforms to simply identify threats. Today, they must support a broader mission: helping organizations understand, prioritize, and reduce risk.
Tools that feed into centralized risk repositories, provide real-time visibility, and integrate across the environment are becoming the standard. Whether you’re assessing the limits of your current EDR platform or exploring the full potential of XDR, the end goal remains the same — smarter, faster, and more strategic risk decisions.
As you move forward, focus on tools that:
- Deliver actionable, context-rich insights
- Support continuous, data-driven risk scoring
- Integrate seamlessly with your existing security stack
- Demonstrate measurable improvement across key performance metrics
Security is not just about technology — it’s about operational effectiveness. And the right tools, evaluated through the right lens, can turn detection into a driver of resilience and strategic advantage.