Too often, companies operate on assumptions instead of clear, measurable data. They check the compliance boxes, run periodic risk assessments, and hope for the best. However, without a structured way to measure risk maturity, you are at the best relying on guesswork and heuristics.
That’s where risk maturity comes in. It’s not just about compliance or having a security framework in place. It’s about truly understanding where your organization stands in terms of risk awareness, preparedness, and resilience. It’s about knowing which threats are critical, which ones need immediate attention, and where to focus your efforts for long-term security.
In this article, we will break down all you need to know about risk maturity and employing a structured approach to measuring and improving risk. Risk is always evolving and so should your approach to managing it. Let’s dive in
What is Risk Maturity and Why Does It Matter?
Risk maturity isn’t just another compliance metric; it’s the foundation of a strong security posture. It tells you how well your organization understands, manages, and mitigates risks in a structured, proactive way.
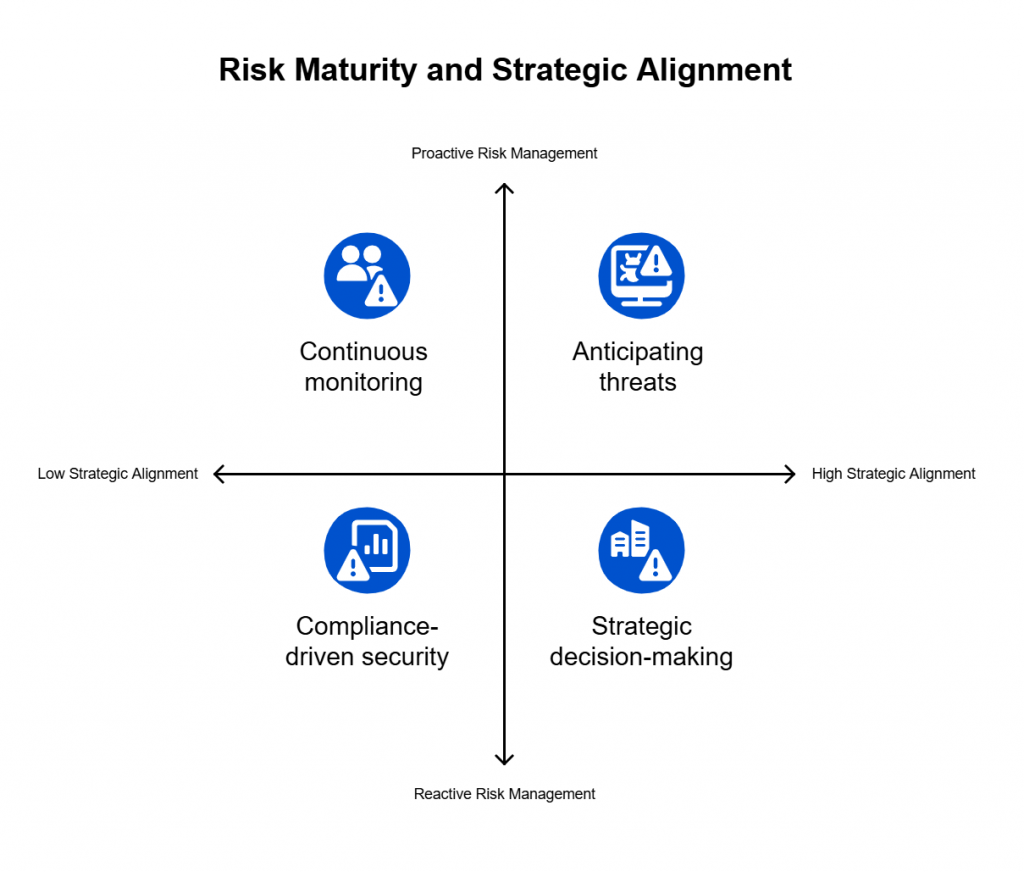
Some companies operate at a basic level of risk maturity, where security is reactive, and risk assessments happen only when auditors come knocking. Others have a high level of maturity, where risk is continuously measured, monitored, and used to drive strategic decision-making.
Here’s why this matters. Organizations with low risk maturity tend to struggle with blind spots, inefficiencies, and missed threats. They might be compliant on paper but fail to see gaps that leave them exposed. On the other hand, companies with high risk maturity don’t just react to threats, they anticipate them. They prioritize security efforts where they matter most, align risk management with business goals, and adapt to evolving threats with confidence.
Think of it like fitness. If you never track your progress, you can’t tell whether your workouts are making a difference. The same applies to cybersecurity—if you’re not actively measuring risk, how do you know if your defenses are improving?
Risk maturity gives you that clarity. It helps you move from reactive to proactive, from compliance-driven to security-driven. And in a world where cyber threats are only getting more sophisticated, guesswork isn’t good enough.
Comparing Risk Maturity Frameworks
Measuring risk maturity isn’t a one-size-fits-all approach. Different organizations have different risk appetites, regulatory requirements, and operational structures. That’s why industry-recognized frameworks exist—to provide structured methodologies for assessing and improving risk management.
Among the most widely used frameworks are NIST Cybersecurity Framework (CSF), ISO 27001, and COBIT. Each one offers a unique perspective on risk maturity, helping organizations understand where they stand and what steps they need to take to strengthen their security posture.
The NIST Cybersecurity Framework focuses on identifying, protecting, detecting, responding to, and recovering from cyber threats. It uses a tiered maturity model ranging from partial to adaptive, making it a flexible and scalable approach for organizations of all sizes. It’s particularly useful for companies looking to improve cybersecurity resilience without rigid compliance mandates.
ISO 27001, on the other hand, is a globally recognized standard for information security management systems. It takes a risk-based approach, helping organizations establish security controls that align with business objectives and regulatory requirements. For companies that need a structured compliance-driven framework, ISO 27001 provides a clear roadmap to reducing risk while maintaining operational efficiency.
COBIT stands out as a governance-first framework, aligning risk management with business objectives. It uses a capability maturity model, ranking organizations from non-existent to optimized in their risk approach. Unlike NIST and ISO 27001, which focus more on cybersecurity controls, COBIT is designed for organizations that want to integrate risk management with IT governance and business strategy.
There’s no single right answer when it comes to choosing a framework. Some organizations use a blend of NIST and ISO 27001 for security and compliance, while others integrate COBIT for a governance-focused approach. What matters most is selecting a framework that aligns with your organization’s risk profile and using it as a foundation to measure and improve risk maturity.
Below is a comparative analysis of some of the most widely used risk maturity frameworks, helping you understand how each one approaches risk and which might be best suited for your organization.
| Framework | Key Focus | Best for Organizations That… | Maturity Assessment Approach |
| NIST Cybersecurity Framework (CSF) | Identifying, protecting, detecting, responding, and recovering from cyber threats | Need a flexible, scalable approach to cybersecurity | Uses a tiered model (Partial → Risk Informed → Repeatable → Adaptive) to assess maturity |
| ISO 27001 | Information security management system (ISMS) compliance | Require a compliance-driven security strategy | Focuses on a risk-based approach to securing assets and meeting compliance |
| COBIT | Governance and risk alignment with business objectives | Need a business-centric IT governance model | Uses a Capability Maturity Model (CMM) approach, ranking from 0 (Non-Existent) to 5 (Optimized) |
| CMMI (Capability Maturity Model Integration) | Process maturity for risk and security management | Need a structured approach to improving risk and security processes over time | Maturity levels range from Initial (ad hoc) to Optimizing (continuous improvement) |
| RMF (Risk Management Framework – NIST 800-37) | Integrating risk management into the system development lifecycle | Need a comprehensive, structured approach to security and compliance | Uses a 6-step process (Categorize, Select, Implement, Assess, Authorize, Monitor) |
Key Metrics to Evaluate Risk Maturity
Selecting a risk framework is just the starting point. To truly understand where your organization stands, you need measurable data that reflects your risk posture in real time. Without clear metrics, risk management can become subjective, reactive, and inefficient.
Organizations that successfully measure risk maturity don’t just track compliance or checkboxes—they quantify risk, prioritize actions based on impact, and continuously refine their security posture.
Here are some of the key metrics that matter when assessing risk maturity:
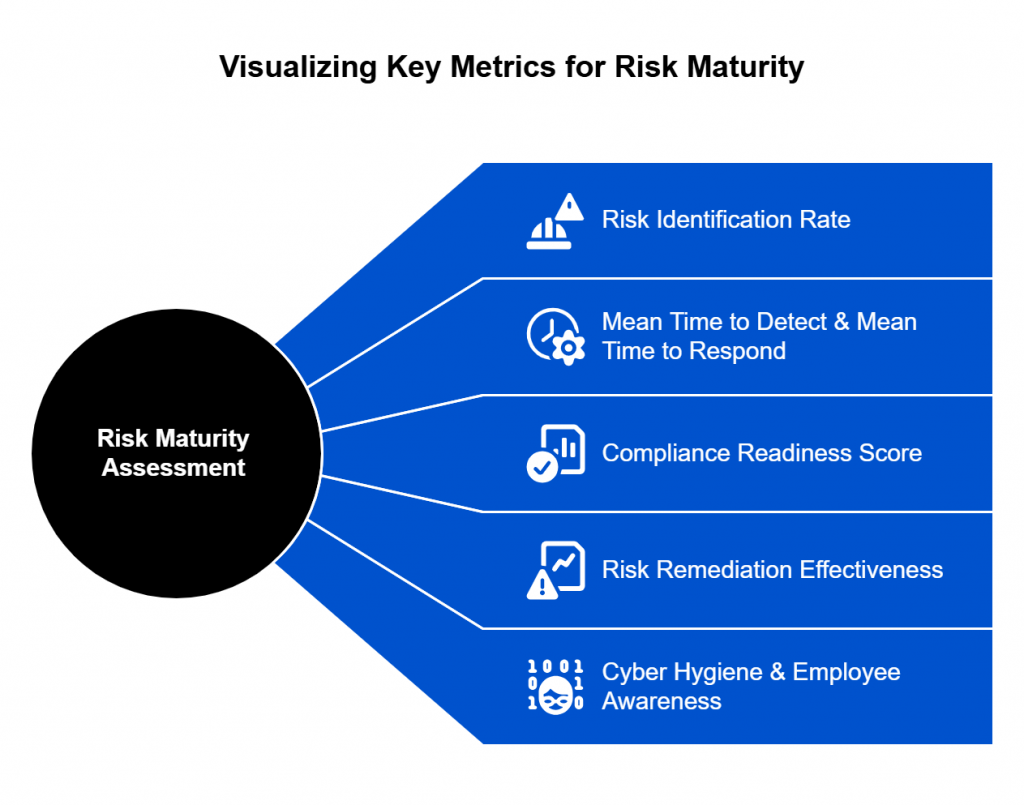
1. Risk Identification Rate
How effectively does your organization detect and classify risks? Measuring the number of identified vulnerabilities, threats, and security gaps over a given period provides insight into the visibility of your risk landscape.
If your risk identification rate is too low, you may not be proactively uncovering threats. If it’s too high and growing, your risk detection capabilities might be improving, but you may lack the resources to address them effectively.
2. Mean Time to Detect (MTTD) & Mean Time to Respond (MTTR)
Speed matters in cybersecurity. The longer a risk or breach goes undetected, the greater the impact.
- MTTD (Mean Time to Detect) measures how quickly your organization identifies a security threat.
- MTTR (Mean Time to Respond) measures how long it takes to mitigate or remediate the issue once detected.
If MTTD is high, your detection tools and processes need improvement. If MTTR is high, your response and remediation strategies may be inefficient.
3. Compliance Readiness Score
Regulatory and industry standards set security baselines, but compliance doesn’t always mean security. Tracking your organization’s compliance with frameworks like ISO 27001, NIST CSF, or RMF helps ensure that security policies align with best practices.
Organizations that track their compliance readiness can proactively address gaps before audits, reducing financial penalties, legal risks, and reputational damage.
4. Risk Remediation Effectiveness
Identifying risks is only the first step—remediation is what truly improves security. This metric evaluates how quickly and effectively an organization patches vulnerabilities or mitigates risks before they can be exploited.
A low remediation rate suggests that security teams are overwhelmed, under-resourced, or lacking automation. Organizations with mature risk management capabilities prioritize and remediate critical risks faster.
5. Cyber Hygiene & Employee Awareness
Even with the best tools, human error remains one of the leading causes of security breaches. Measuring employee security awareness and cyber hygiene through phishing simulations, password management audits, and policy compliance checks helps gauge the human factor in your risk maturity.
If employees consistently fail security tests, your organization is at higher risk of social engineering attacks. High-risk industries (like finance and healthcare) should prioritize continuous security training to reduce insider threats.
Common Pitfalls in Measuring Risk Maturity—and How to Avoid Them
Even with the right frameworks and metrics in place, organizations often fall into traps that limit the effectiveness of their risk maturity assessments. These missteps can lead to a false sense of security, misallocated resources, and increased exposure to threats.
Understanding these pitfalls ensures that risk assessments translate into real security improvements, not just compliance checkboxes.
Confusing Compliance with Security
One of the most common mistakes is assuming that passing an audit means an organization is secure. Many focus heavily on meeting regulatory requirements like ISO 27001 or NIST but fail to adopt a risk-based approach that actively improves security.
Compliance provides a baseline, but it doesn’t mean threats have been mitigated. Organizations need to go beyond compliance checklists and use risk scoring and continuous monitoring to identify actual security weaknesses.
Relying on Manual Risk Assessments
Manual assessments are slow, error-prone, and quickly outdated. They rely on static reports that don’t reflect real-time risks, making it difficult to detect threats as they emerge.
Automated risk assessment tools provide continuous monitoring and real-time scoring of vulnerabilities, threats, and control effectiveness. This shift from static reports to dynamic insights helps security teams respond faster and more effectively.
Ignoring Risk Prioritization
Not all risks are equal, yet some security teams treat every vulnerability as equally critical. This approach overwhelms resources and delays the resolution of high-impact threats. A risk-based approach prioritizes threats based on impact, exploitability, and business criticality. Aligning risk remediation efforts with what matters most to the organization ensures that the most dangerous threats are addressed first.
Lack of Executive Buy-In
Risk management isn’t just an IT responsibility—it’s a business issue. Without leadership support, security teams struggle to get the budget, tools, and authority needed to improve risk maturity.
Communicating risk in business terms is essential. Instead of discussing vulnerabilities in technical language, security leaders should focus on financial impact, regulatory consequences, and reputational damage. Demonstrating how security investments reduce risk and strengthen business resilience helps gain executive support.
No Clear Ownership of Risk Management
Risk management often falls into a gray area where no single team has full responsibility. IT security, compliance, and risk teams operate independently, leading to fragmented risk assessment efforts.
Defining clear ownership and accountability for risk management is crucial. Cross-functional collaboration between security, compliance, IT, and business leaders ensures a unified approach.
Measuring Risk Too Infrequently
Risk is constantly changing. If an organization assesses risk only annually or quarterly, it risks missing the rapid shifts in threat landscapes, new vulnerabilities, and changes in business operations.
Moving from point-in-time assessments to continuous risk monitoring helps security teams stay informed about risk exposure in real time. Automated risk scoring allows organizations to detect changes as they happen and adapt accordingly.
Building a Roadmap for Risk Maturity Advancement
Understanding risk maturity is just the beginning. The real challenge lies in transforming insights into action. Organizations that successfully advance their risk maturity do so by creating a structured, measurable roadmap that aligns security efforts with business priorities.
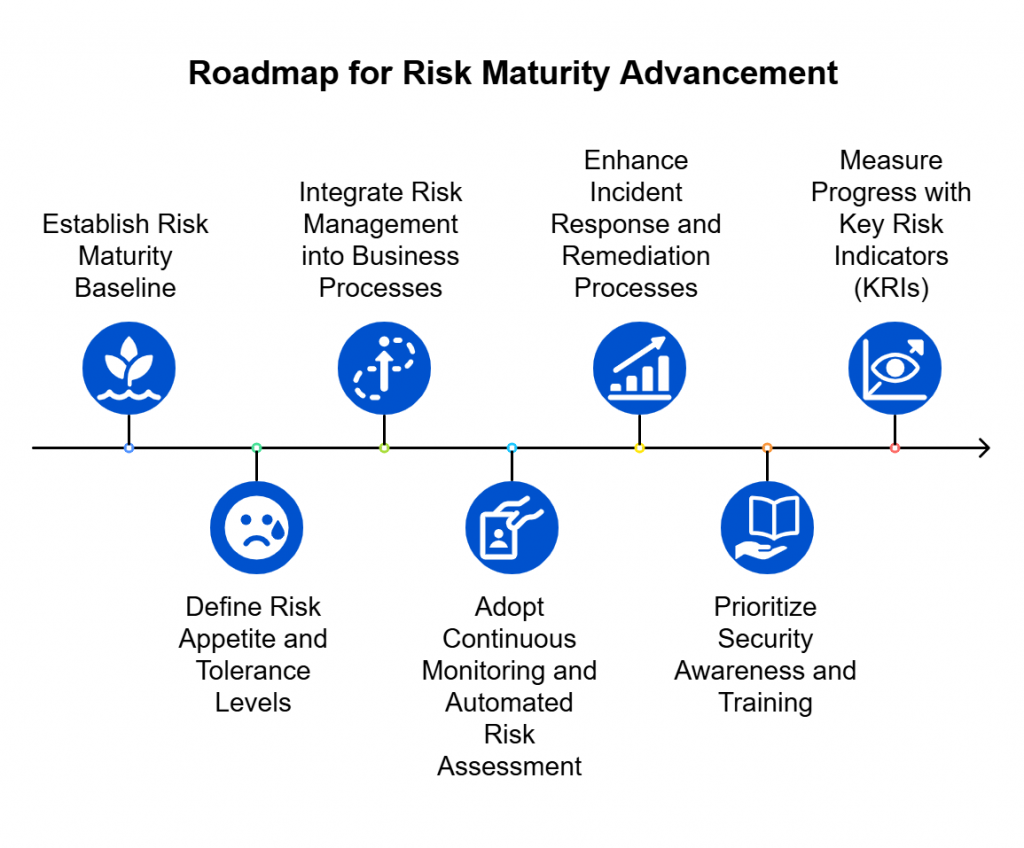
- Establish a Clear Risk Maturity Baseline
Before making improvements, organizations need a realistic assessment of their current risk posture. This involves conducting a comprehensive risk assessment using established frameworks like NIST CSF, ISO 27001, or COBIT. Automated risk scoring can provide a more objective, data-driven view of vulnerabilities, helping to eliminate blind spots. - Define Risk Appetite and Tolerance Levels
Not all risks can or should be eliminated. Organizations need to determine how much risk they are willing to accept in different areas of the business. Clearly defining risk appetite allows security teams to focus on high-priority threats while ensuring that controls remain aligned with operational and financial objectives. - Integrate Risk Management into Business Processes
Risk maturity isn’t just about cybersecurity—it must be woven into the organization’s overall business strategy. Security leaders should work closely with compliance, legal, IT, and executive teams to ensure risk management is not viewed as a standalone function but as a critical part of business resilience and growth. - Adopt Continuous Monitoring and Automated Risk Assessment
Traditional risk assessments, conducted annually or quarterly, no longer keep pace with today’s evolving threat landscape. Organizations need to shift to real-time risk monitoring using automated tools that track vulnerabilities, measure control effectiveness, and provide actionable insights. Continuous risk assessment allows for faster response times and better decision-making. - Enhance Incident Response and Remediation Processes
Improving risk maturity isn’t just about identifying threats—it’s about responding to them effectively. Organizations should refine their incident response plans to ensure that security teams can contain, investigate, and mitigate risks efficiently. Conducting regular tabletop exercises and red team simulations can help test and strengthen these processes. - Prioritize Security Awareness and Training
A well-informed workforce is one of the strongest defenses against cyber threats. Organizations should invest in continuous security awareness programs that educate employees on recognizing phishing attempts, social engineering tactics, and other security risks. When employees understand their role in risk management, the organization as a whole becomes more resilient. - Measure Progress with Key Risk Indicators (KRIs)
Advancing risk maturity requires tracking progress over time. Organizations should establish clear risk maturity metrics, such as mean time to detect (MTTD), mean time to respond (MTTR), compliance adherence rates, and remediation effectiveness. Regularly reviewing these metrics ensures that improvements are data-driven and aligned with business goals.
The Path Forward
Risk maturity isn’t a final destination—it’s an ongoing process of improvement. Organizations that build a structured roadmap and commit to continuous assessment and adaptation will be better positioned to navigate the evolving threat landscape. By integrating security into business strategy, leveraging automation, and prioritizing proactive risk management, companies can shift from reacting to threats to staying ahead of them.
A mature risk posture means being prepared, adaptable, and resilient. The question isn’t whether an organization will face cyber risks—it’s how well prepared it will be when they arise.
