In fact, a 2023 survey revealed that nearly 70% of service organizations needed to demonstrate compliance with at least six different frameworks covering information security and data privacy. This statistic underscores the increasing complexity and breadth of regulatory requirements that organizations must navigate.
Businesses must take a smarter approach to manage compliance. You can take control by aligning common requirements, reducing redundant work, and staying ahead of regulatory changes. This article explores how to navigate multiple frameworks efficiently and eliminate unnecessary work.
Overview of Overlapping Requirements and Controls
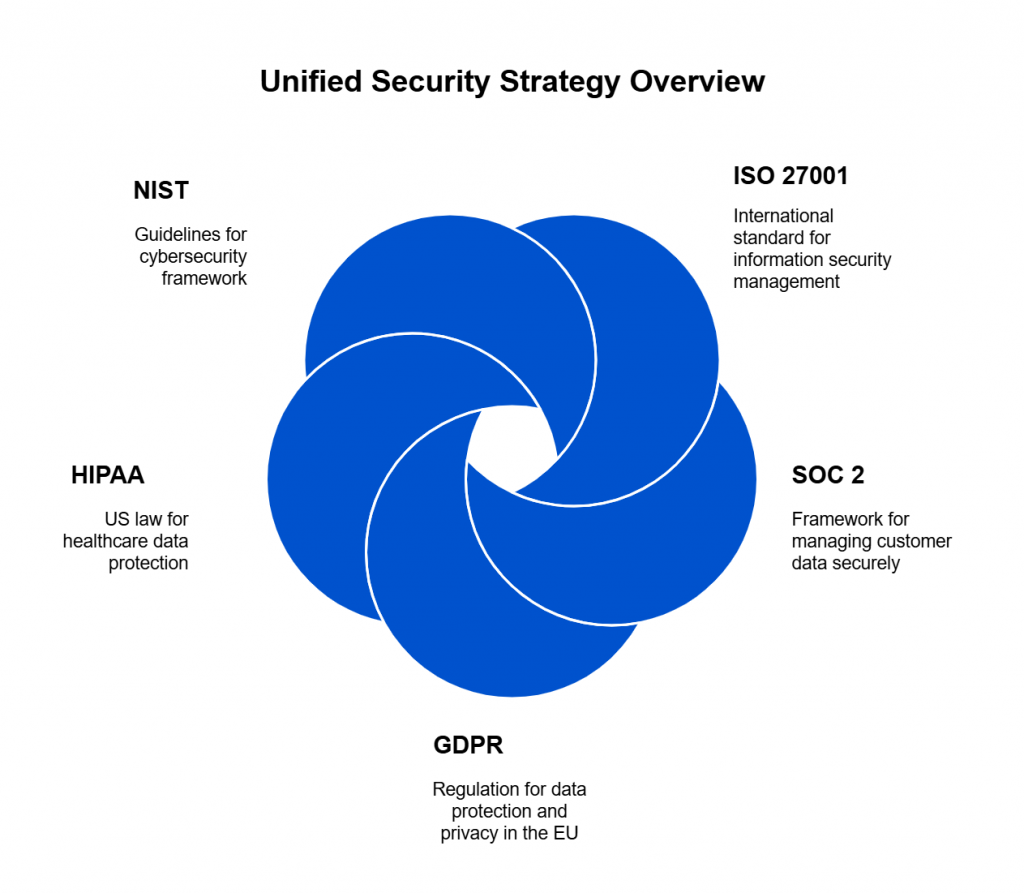
Managing multiple security and privacy frameworks can feel like juggling different rulebooks for the same game. Each framework sets unique compliance standards, but many share similar requirements. Instead of treating them as separate checklists, organizations can streamline compliance by identifying commonalities and implementing a unified security strategy. This approach not only reduces the burden on security and compliance teams but also strengthens overall cybersecurity posture.
Why Do Frameworks Overlap?
Security and privacy regulations exist to protect sensitive information and mitigate risks. Since cyber threats and data protection challenges remain consistent across industries, frameworks like ISO 27001, SOC 2, GDPR, HIPAA, and NIST introduce overlapping controls to address similar risks.
For example:
- ISO 27001 focuses on an information security management system (ISMS) to protect data assets.
- SOC 2 emphasizes controls for safeguarding customer data in cloud environments.
- GDPR prioritizes personal data protection and privacy rights.
- NIST Cybersecurity Framework (CSF) provides best practices for risk management.
Though their scopes may differ, these frameworks often align in key security areas.
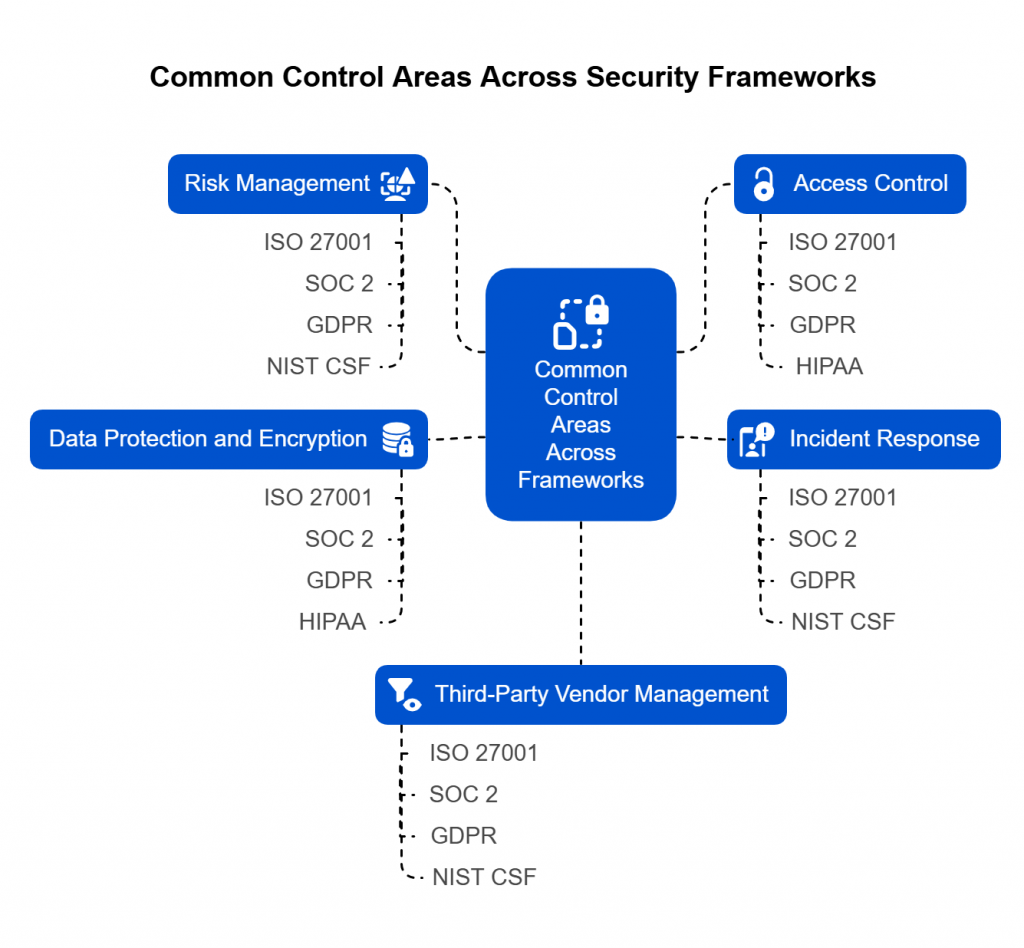
Common Control Areas Across Frameworks
Most security and privacy frameworks share fundamental principles. By understanding these similarities, organizations can consolidate compliance efforts, reduce redundant tasks, and optimize security investments.
- Risk Management
- ISO 27001: Requires businesses to conduct a formal risk assessment and create a risk treatment plan.
- SOC 2: Includes risk-based security controls to ensure system reliability.
- GDPR: Mandates businesses to apply risk-based security measures when handling personal data.
- NIST CSF: Focuses on continuous risk assessment and mitigation strategies.
Key takeaway: A single risk management framework can satisfy multiple standards. Organizations can implement one structured process and map it across different compliance frameworks.
- Access Control
- ISO 27001: Enforces least privilege access and authentication controls.
- SOC 2: Requires strong access management to protect sensitive data.
- GDPR: Emphasizes role-based access and data minimization.
- HIPAA: Requires authentication and access logs to safeguard electronic health records.
Key takeaway: A unified Identity and Access Management (IAM) system with multi-factor authentication (MFA), role-based access, and periodic access reviews can fulfill multiple compliance requirements.
- Incident Response
- ISO 27001: Requires organizations to establish an incident management process.
- SOC 2: Mandates a structured incident response plan.
- GDPR: Imposes a 72-hour breach notification rule.
- NIST CSF: Provides guidelines for incident detection, response, and recovery.
Key takeaway: A centralized incident response plan with clear reporting procedures can help organizations comply with multiple frameworks while improving resilience against cyber threats.
- Data Protection and Encryption
- ISO 27001: Requires organizations to encrypt sensitive information.
- SOC 2: Mandates encryption for data at rest and in transit.
- GDPR: Urges businesses to apply encryption and pseudonymization to protect personal data.
- HIPAA: Requires encryption for electronic protected health information (ePHI).
Key takeaway: A comprehensive data encryption policy that includes strong cryptographic controls, key management, and secure storage can satisfy multiple compliance frameworks.
- Third-Party Vendor Management
- ISO 27001: Requires organizations to assess and monitor supplier risks.
- SOC 2: Includes vendor risk management as part of security controls.
- GDPR: Holds businesses accountable for third-party data processors.
- NIST CSF: Recommends continuous vendor risk assessments.
Key takeaway: A centralized third-party risk management program with standardized due diligence, contract reviews, and ongoing monitoring can cover multiple regulatory requirements.
The Benefits of Recognizing Overlaps
Identifying commonalities across compliance frameworks helps organizations:
- Reduce duplication: A single policy, control, or report can satisfy multiple requirements.
- Streamline audits: Cross-mapping controls minimizes redundant audit requests.
- Improve efficiency: Security teams can focus on risk management rather than chasing multiple compliance checklists.
- Strengthen security: A holistic approach enhances protection beyond just compliance.
Instead of treating each requirement separately, businesses can map overlapping controls and develop a single, cohesive compliance strategy.
Strategies for Unifying Evidence Across Frameworks
Managing compliance with multiple frameworks can feel like a never-ending paper trail. Organizations must collect evidence for audits, security assessments, and regulatory reviews—often repeating the same work for different frameworks. Without a structured approach, compliance teams waste time gathering redundant documentation, responding to multiple audit requests, and managing overlapping controls.
Instead of handling each framework separately, organizations can take a centralized approach to unify evidence collection. This strategy streamlines compliance efforts, reduces duplication, and ensures that security controls remain consistent across frameworks.
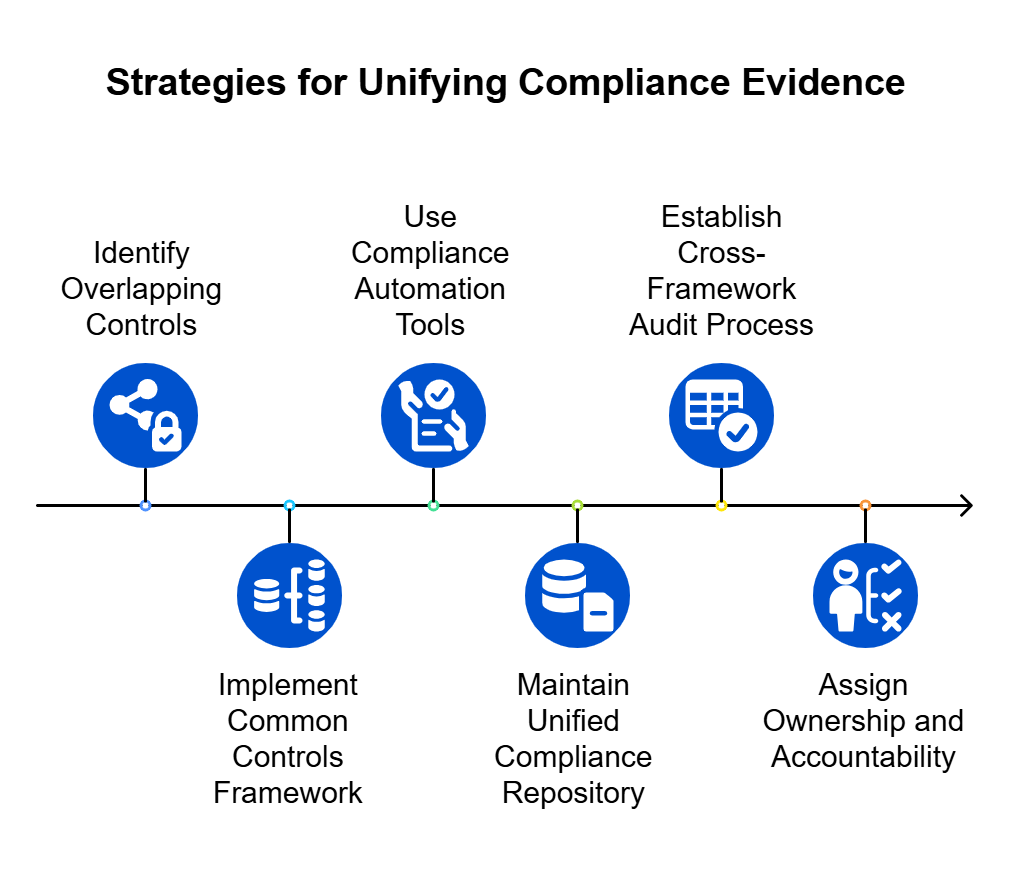
1. Implement a Common Controls Framework (CCF)
A Common Controls Framework (CCF) maps shared security and compliance requirements across multiple standards. This approach enables organizations to test, document, and report on controls once while applying the evidence to multiple frameworks.
How it works:
- Identify overlapping controls (e.g., access control, encryption, risk management).
- Align each control to multiple frameworks (e.g., ISO 27001, SOC 2, GDPR, NIST).
- Store evidence in a central repository for reuse across audits.
Example:
- A single access control policy can serve as evidence for ISO 27001 (A.9.1.1), SOC 2 (CC6.1), and GDPR (Article 32).
- A unified risk assessment process can fulfill ISO 27001 (A.6.1.2), SOC 2 (CC3.2), and GDPR (Article 35).
By implementing a CCF, organizations can eliminate redundant work and ensure consistency across compliance efforts.
2. Use Compliance Automation Tools
Manually tracking compliance evidence across multiple frameworks leads to inefficiencies and errors. Modern compliance automation platforms simplify the process by allowing organizations to:
- Collect and centralize evidence in one system.
- Automatically map controls to multiple frameworks.
- Generate audit-ready reports on demand.
Tools like Spog.AI help organizations manage compliance more efficiently.
Example:
- Upload a vendor risk assessment once and link it to both ISO 27001 and SOC 2 requirements.
- Use automated access reviews to satisfy multiple frameworks simultaneously.
Automation reduces manual tracking, saves time, and ensures that compliance teams stay ahead of audits.
3. Maintain a Unified Compliance Repository
A centralized compliance repository acts as a single source of truth for all security policies, risk assessments, incident reports, and audit evidence. Organizations can store:
- Security policies (e.g., access control, data protection, incident response).
- Risk assessment documentation (aligned with multiple frameworks).
- Audit reports and certifications (SOC 2, ISO 27001, penetration testing).
- Vendor security assessments (for third-party compliance).
How to implement it:
- Use document management systems like SharePoint, Confluence, or a GRC (Governance, Risk, and Compliance) tool like Spog.AI.
- Standardize evidence collection with predefined templates and compliance calendars.
A centralized repository prevents teams from scrambling for documents before audits and ensures easy retrieval of compliance evidence.
4. Establish a Cross-Framework Audit Process
Instead of conducting separate audits for each framework, organizations can streamline the process by:
- Aligning internal audits with multiple compliance standards.
- Conducting one comprehensive assessment that covers multiple frameworks.
- Using shared control testing procedures to reduce redundant audit work.
Example:
- A single penetration test can provide evidence for SOC 2, ISO 27001, and GDPR security controls.
- A unified internal audit process can simultaneously assess compliance with multiple frameworks.
Organizations can reduce audit fatigue and optimize compliance operations.
5. Assign Ownership and Accountability
Without clear ownership, compliance efforts become scattered, leading to inconsistencies and duplicated work. To streamline compliance, organizations should:
- Assign dedicated owners for security controls and policies.
- Define roles and responsibilities for evidence collection and audit management.
- Establish a cross-functional compliance team that includes security, IT, legal, and risk management personnel.
Assigning accountability ensures that compliance efforts remain structured, efficient, and audit-ready.
Tips for Avoiding Duplication: Cross-Mapping Controls
Managing compliance across multiple frameworks can feel like solving the same puzzle in different ways. Without a structured approach, organizations end up duplicating efforts—writing multiple policies for similar controls, performing redundant audits, and collecting the same evidence multiple times. Cross-mapping controls eliminates this inefficiency by aligning security measures across different frameworks, allowing organizations to manage compliance more effectively.
By leveraging cross-mapping techniques, businesses can reduce workload, minimize audit fatigue, and ensure consistent security practices across various compliance requirements.
1. Develop a Control Mapping Matrix
A control mapping matrix aligns similar requirements across multiple frameworks. Instead of treating each standard as a separate checklist, organizations can map overlapping controls and apply a single policy, procedure, or control to multiple frameworks.
How to Create a Control Mapping Matrix
- Identify common requirements
- Group similar security controls (e.g., risk management, access control, incident response).
- Map each requirement across frameworks
- Align the requirements of ISO 27001, SOC 2, GDPR, NIST, HIPAA, and others.
- Maintain a centralized reference document
- Use spreadsheets, GRC (Governance, Risk, and Compliance) platforms, or compliance automation tools.
Example: Control Mapping for Access Control
| Control Area | ISO 27001 | SOC 2 | GDPR | NIST CSF | HIPAA |
| Identity & Access Management | A.9.2.1 | CC6.1 | Article 32 | PR.AC-1 | 164.312(a)(1) |
| Least Privilege | A.9.4.1 | CC6.3 | Article 25 | PR.AC-6 | 164.308(a)(4) |
| Multi-Factor Authentication (MFA) | A.9.3.1 | CC6.2 | Recommended | PR.AC-7 | Recommended |
Key Benefit: A single access control policy can satisfy multiple frameworks, reducing duplication and ensuring compliance across different standards.
2. Establish a Unified Set of Policies and Procedures
Many organizations create separate security policies for different frameworks, leading to redundant documentation and inconsistencies. Instead of maintaining multiple versions of the same policy, businesses should develop a single, unified set of security policies that reference multiple frameworks.
How to Consolidate Policies
- Write one security policy that aligns with multiple compliance requirements.
- Include references to relevant frameworks in each section.
- Ensure audit teams recognize the mapped policies as valid evidence across multiple standards.
Example: Data Protection Policy
A single Data Protection Policy can be structured as follows:
- Section 1: Encryption Standards
- ISO 27001 (A.10.1.1)
- SOC 2 (CC6.8)
- GDPR (Article 32)
- Section 2: Data Retention
- ISO 27001 (A.8.3.2)
- GDPR (Article 5)
- HIPAA (45 CFR §164.316)
Key Benefit: A single document can meet multiple compliance needs, reducing duplication and simplifying policy management.
3. Leverage Audit Evidence Across Multiple Standards
Organizations often perform separate audits for different frameworks, even when they require similar evidence. By aligning audit cycles and sharing documentation, businesses can reduce redundant work.
How to Optimize Audit Evidence
- Reuse risk assessments across multiple standards (ISO 27001, SOC 2, NIST, GDPR).
- Share penetration test reports across SOC 2, ISO 27001, and GDPR audits.
- Align security awareness training programs to meet compliance for ISO 27001, SOC 2, and HIPAA.
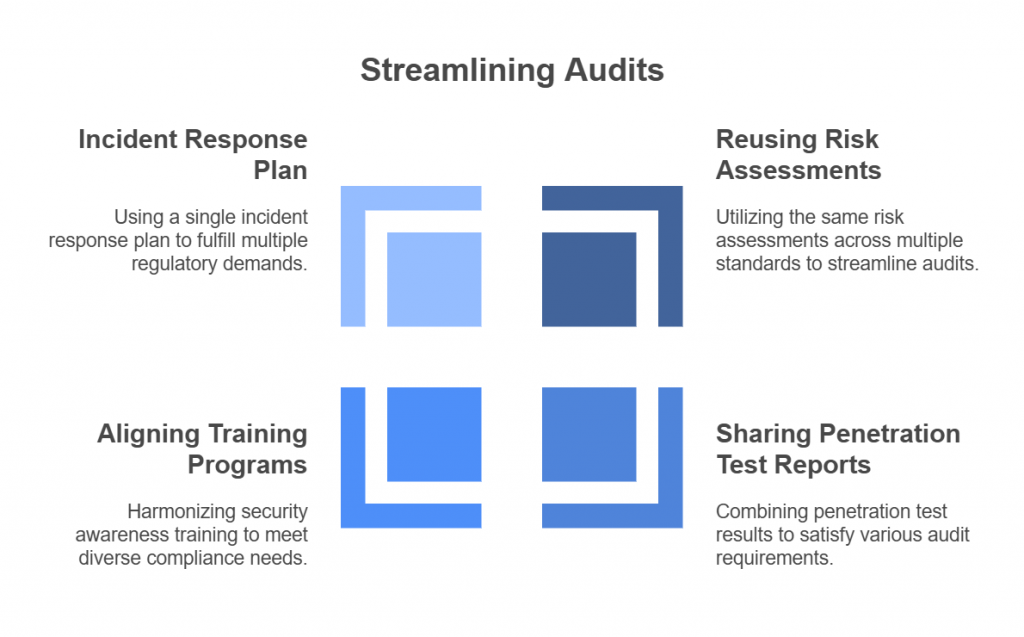
Example: Incident Response Plan as Evidence
A single Incident Response Plan (IRP) can provide evidence for:
- ISO 27001 (A.16.1.1)
- SOC 2 (CC7.2)
- GDPR (Article 33 – Breach Notification)
- NIST CSF (RS.RP-1)
Key Benefit: Organizations can save time, reduce audit costs, and minimize operational disruptions by using one set of evidence for multiple compliance frameworks.
4. Use Compliance Automation and GRC Tools
Manually tracking cross-mapped controls can be overwhelming. Compliance automation tools simplify the process by allowing organizations to:
- Automatically map controls across multiple frameworks.
- Store policies, procedures, and audit evidence in a centralized platform.
- Generate reports that demonstrate compliance across standards.
Popular Compliance Tools for Cross-Mapping
- Spog.AI – Pulls data from both on-premises and cloud solutions to centralize evidence collection across popular global cyber security and information security frameworks.
- Drata – Maps SOC 2, ISO 27001, HIPAA, GDPR, and NIST.
- Vanta – Automates evidence collection for multiple frameworks.
- Hyperproof – Provides a control-mapping dashboard.
- OneTrust – Specializes in GDPR, CCPA, and privacy compliance.
Key Benefit: Automation eliminates human error, speeds up compliance, and makes audits more efficient.
5. Align Internal Compliance Reviews Across Frameworks
Instead of separate compliance reviews for each framework, organizations should schedule one internal audit that assesses multiple standards simultaneously.
How to Align Compliance Reviews
- Perform a single risk assessment that addresses ISO 27001, SOC 2, and GDPR.
- Conduct unified security testing (e.g., penetration tests, vulnerability scans) and map results across frameworks.
- Prepare one compliance report with control mappings instead of multiple reports for different audits.
Example: Annual Compliance Review Strategy
| Review Activity | ISO 27001 | SOC 2 | GDPR | NIST CSF |
| Risk Assessment | Yes | Yes | Yes | Yes |
| Penetration Testing | Yes | Yes | No (recommended) | Yes |
| Security Awareness Training | Yes | Yes | Yes | Yes |
| Vendor Risk Management | Yes | Yes | Yes | Yes |
Key Benefit: By synchronizing compliance efforts, businesses can reduce audit preparation time, lower costs, and improve security effectiveness.
Cross-mapping compliance controls eliminates unnecessary duplication, reduces costs, and streamlines security efforts. Organizations that implement a control mapping matrix, consolidate policies, align audit cycles, and leverage automation can significantly improve efficiency while maintaining a strong security and compliance posture.
Handling Updates as Regulations Evolve
Compliance isn’t a one-time effort—it’s a continuous process. As governments introduce new regulations and industry standards evolve, businesses must stay ahead of compliance changes to avoid penalties, security gaps, and operational disruptions. However, tracking and adapting to evolving frameworks like ISO 27001, SOC 2, GDPR, NIST, HIPAA, and new privacy laws can be overwhelming.
To maintain compliance, organizations need a proactive approach that includes regulatory monitoring, structured change management, continuous assessments, and automation-driven tracking. This section explores key strategies to keep compliance efforts up to date.
1. Stay Informed with Regulatory Monitoring
Laws and compliance frameworks frequently update to address emerging cybersecurity threats, technological advancements, and evolving privacy concerns. Organizations that fail to monitor these changes risk falling behind and facing compliance violations.
How to Stay Updated
- Subscribe to official regulatory updates
- Join industry groups and compliance communities
- Cloud Security Alliance (CSA)
- International Association of Privacy Professionals (IAPP)
- Information Systems Audit and Control Association (ISACA)
- Monitor regulatory enforcement cases
- Follow GDPR fines and SOC 2 audit reports to understand how regulators interpret and enforce compliance requirements.
Staying informed prevents last-minute compliance scrambles and helps organizations plan ahead for regulatory shifts.
2. Implement a Compliance Change Management Process
Many organizations struggle to integrate regulatory updates into their existing security and compliance frameworks. A compliance change management process ensures smooth transitions when new regulations take effect.
How to Manage Compliance Updates
- Establish a Compliance Task Force
- Assign a dedicated team responsible for tracking and implementing regulatory changes.
- Assess the Impact of New Regulations
- Determine whether an update affects policies, security controls, or operational processes.
- Update Policies and Procedures
- Modify security policies to align with new compliance requirements.
- Train employees on revised procedures to ensure company-wide adherence.
- Communicate Changes to Stakeholders
- Inform internal teams, vendors, and auditors about policy adjustments.
- Audit and Validate Compliance Adjustments
- Conduct internal reviews to ensure the organization meets updated requirements.
A structured change management process reduces compliance gaps and minimizes disruptions when frameworks evolve.
3. Conduct Continuous Compliance Assessments
Regulations don’t change overnight, but organizations that wait for annual audits often struggle to adapt to new compliance requirements. Continuous compliance assessments help businesses identify gaps early and take corrective action before audits or regulatory deadlines.
Best Practices for Continuous Compliance
- Perform regular gap analyses – Compare existing controls against new or revised compliance requirements.
- Use real-time compliance monitoring tools- Automated platforms like Spog.AI track compliance status continuously.
- Schedule quarterly internal audits – Instead of waiting for an annual audit, conduct mini-audits to test compliance throughout the year.
- Engage third-party auditors for pre-audit assessments – External consultants can help identify compliance blind spots before formal audits.
Continuous assessments prevent compliance surprises and allow organizations to make timely improvements.
4. Auto-Update Regulatory Rule Engine for Compliance Management
Tracking regulatory changes manually is inefficient, time-consuming, and prone to errors. An Auto-Update Regulatory Rule Engine solves this problem by automatically integrating new compliance requirements into an organization’s governance framework.
How the Auto-Update Rule Engine Works
- Automated Regulatory Tracking : The engine continuously scans legal databases, government publications, and compliance repositories for updates.
- Intelligent Control Mapping: It cross-references new regulations with existing policies and security controls to identify necessary changes.
- Automated Policy Adjustments: The system flags outdated policies and recommends updates based on new compliance rules.
- Compliance Impact Analysis: Organizations receive real-time alerts on how regulatory changes affect their operations and security controls.
- Seamless Integration with GRC Platforms: The engine syncs with Governance, Risk, and Compliance (GRC) tools to ensure automatic compliance tracking.
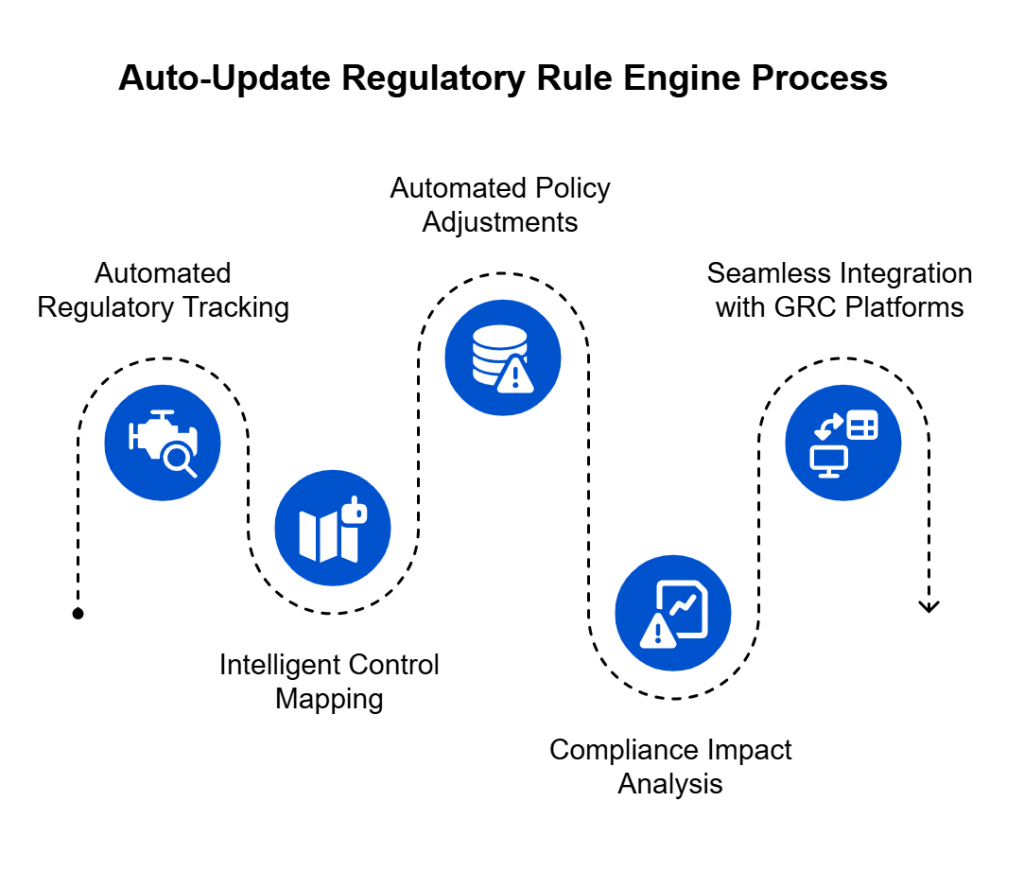
Example Use Case: GDPR & AI Regulations
- Suppose the EU introduces a new AI privacy regulation under GDPR.
- The Auto-Update Regulatory Rule Engine detects the new law and maps it to the existing data processing and risk assessment policies.
- The system alerts compliance officers, recommending necessary changes to ensure alignment with the updated GDPR requirements.
This automated approach reduces manual effort, enhances accuracy, and ensures businesses stay compliant without last-minute rushes.
5. Future-Proof Compliance by Designing Scalable Policies
New regulations will continue to emerge as cybersecurity threats evolve. Instead of constantly rewriting policies, organizations should develop scalable security and compliance frameworks that adapt to future changes without major overhauls.
How to Build Scalable Compliance Policies
- Use a principles-based approach: Instead of writing compliance policies for a specific framework (e.g., SOC 2), define broad security principles that apply across multiple frameworks.
- Adopt modular compliance controls: Design security controls that can be easily adjusted to meet new requirements.
Example: Implementing zero-trust architecture now can future-proof access control policies for upcoming regulations.
- Maintain a flexible risk assessment process: Allow risk assessments to adapt as new threats and compliance requirements emerge.
Scalable compliance policies reduce the need for constant rewrites and allow organizations to quickly adapt to new frameworks.
Conclusion: Turning Compliance into a Strategic Advantage
Navigating multiple compliance frameworks is often seen as a burden—a maze of overlapping regulations, endless audits, and ever-changing requirements. But organizations that approach compliance strategically can transform it from an operational headache into a powerful competitive advantage.
The key to mastering compliance lies in alignment, automation, and adaptability. Instead of managing each framework separately, businesses must recognize the common threads that connect them. A well-structured compliance program unifies controls, eliminates redundancy, and ensures security remains at the core of every decision. Companies that build compliance into their DNA—rather than treating it as an afterthought—will not only meet regulatory expectations but also strengthen customer trust, streamline operations, and stay ahead of evolving threats.
The future of compliance belongs to organizations that embrace innovation. Automation tools, AI-driven regulatory tracking, and Auto-Update Regulatory Rule Engines are reshaping how businesses handle compliance. The companies that invest in continuous assessments, proactively adjust policies, and integrate real-time compliance monitoring will be the ones that lead their industries in security, trust, and efficiency.
In an era where data breaches, regulatory fines, and reputational risks are increasing, compliance is no longer optional—it’s a business imperative. Those who approach it with a reactive mindset will struggle, but those who see compliance as a driver of security, efficiency, and competitive differentiation will thrive. The question is no longer whether you need to comply, but how effectively and strategically you can do it.
