In 2017, one of the world’s largest credit reporting agencies suffered a massive data breach that exposed the personal information of nearly 148 million people. Hackers exploited a known vulnerability in a web application—one that had been left unpatched for months. This allowed them to steal Social Security numbers, birth dates, addresses, and credit card details. The company discovered the breach in July but didn’t publicly disclose it until September, sparking outrage and government investigations. The consequences were severe: the company faced hundreds of millions in settlements, its stock price crashed, and its reputation took a serious hit. Yet, this breach wasn’t caused by an advanced, never-before-seen exploit. It happened because a fixable vulnerability was ignored.
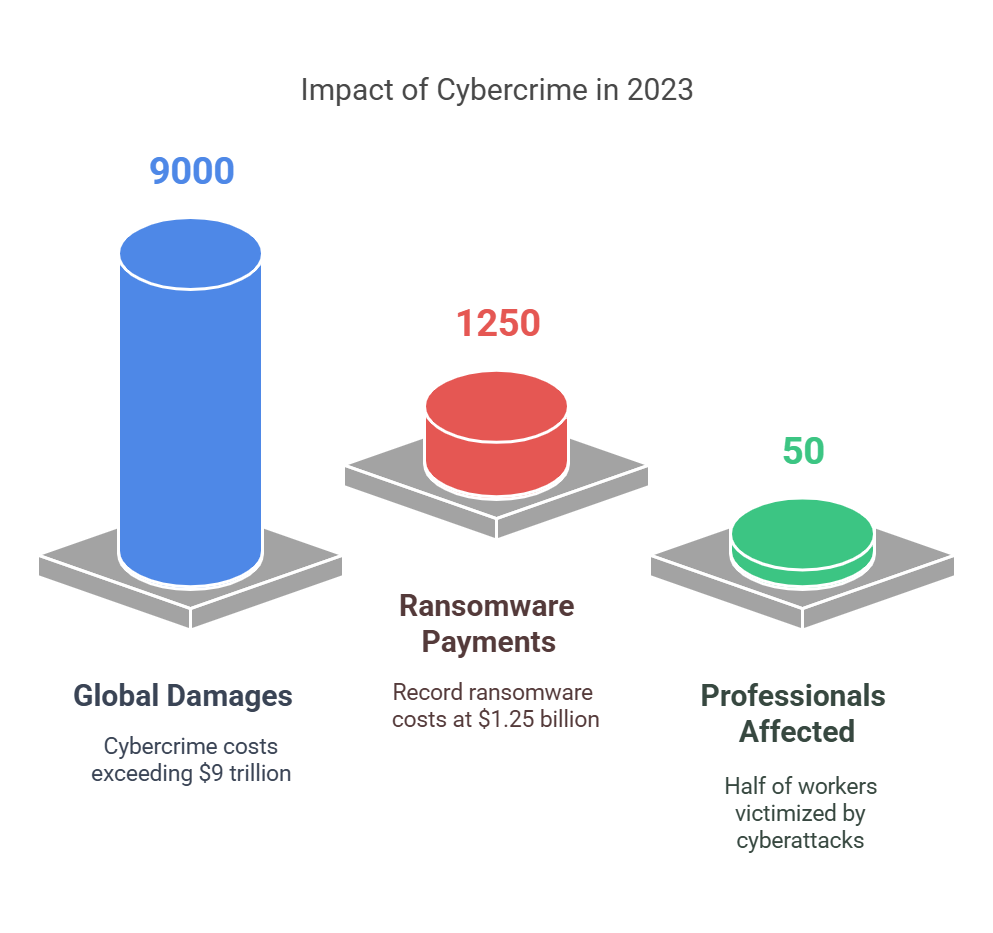
This real-world incident is one of many that have shaken the industry. Lessons have been learned, but cyber threats keep evolving. Attacks are becoming more frequent, more costly, and more complex. In 2023, cybercrime inflicted damages of over $9 trillion globally, while ransomware payments reached a record-breaking $1.25 billion. Nearly half of all working professionals have fallen victim to cyberattacks or scams, proving that no one is immune. Yet, despite these alarming numbers, many organizations still struggle to measure and prioritize cyber risks effectively.
Traditional security measures—firewalls, antivirus software, and routine patching—are no longer enough to stop modern threats. Cybercriminals are faster, smarter, and more coordinated than ever. Organizations must move beyond reactive defenses and adopt a proactive, data-driven strategy. This means using threat intelligence, predictive analytics, and risk modeling to understand security weaknesses before they are exploited.
The real challenge lies in managing the overwhelming flood of security data. Every day, organizations generate massive amounts of information—vulnerability scans, SIEM logs, and real-time threat feeds. Without the right tools to analyze and prioritize risks, security teams can become buried under data, allowing critical threats to slip through unnoticed. To stay ahead, businesses must quantify cyber threats using structured methods that assign risk scores based on real-world attack probabilities.
The Importance of Actionable Threat Intelligence
Cybersecurity is no longer just about setting up firewalls and waiting for alerts. Attackers are constantly evolving, using new methods to bypass defenses. The key to staying ahead is threat intelligence, but raw data alone isn’t enough. Organizations must turn information into actionable insights that help prevent attacks before they happen.
Many companies collect intelligence but don’t know how to use it effectively. This leads to information overload, where security teams struggle to identify real threats among thousands of alerts. Without a clear strategy, businesses waste time chasing false positives while serious risks go unnoticed.
To maximize its impact, threat intelligence must be timely, relevant, and easy to apply. Here’s how organizations can make it actionable:
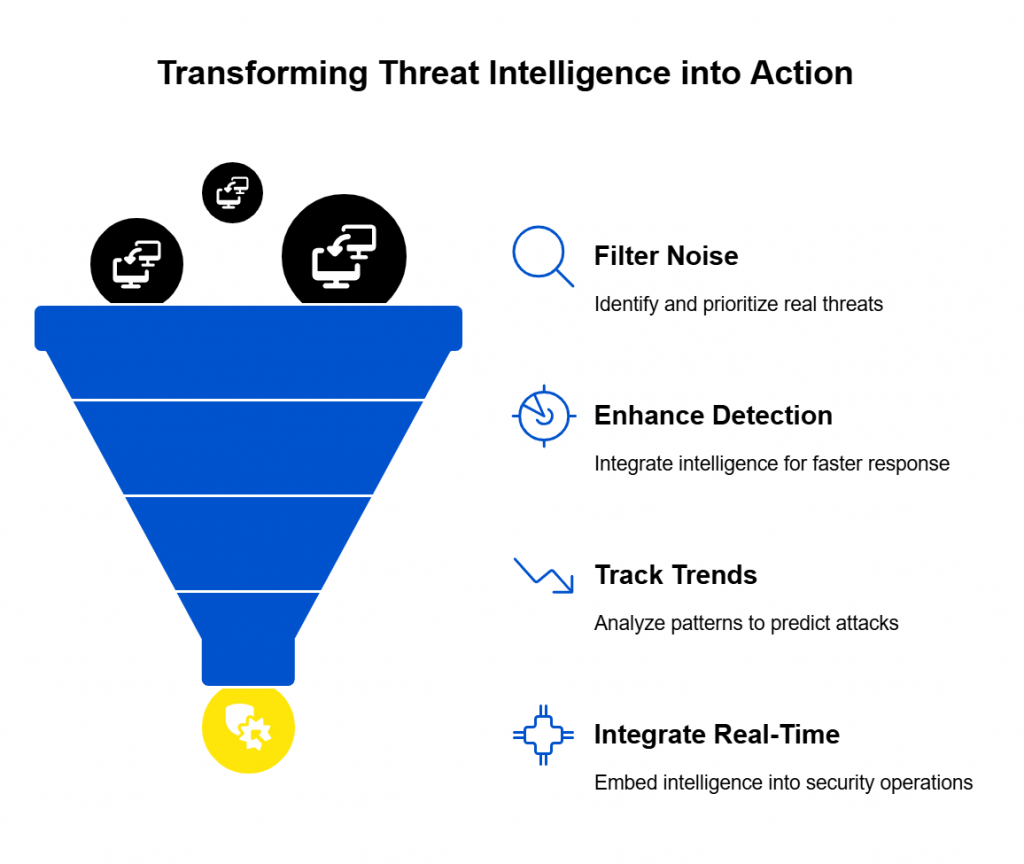
1. Filtering Noise: Separating Real Threats from False Alerts
Every day, security systems generate thousands of alerts. The challenge is knowing which ones matter. Without proper filtering, teams can waste valuable time on low-priority issues while attackers exploit high-risk vulnerabilities.
To reduce noise and focus on critical threats:
- Use risk-based prioritization: Focus on vulnerabilities that are actively exploited in the wild.
- Leverage external intelligence: Cross-check alerts against threat feeds to see if attackers are actively using certain exploits.
- Automate filtering: Use security tools to rank alerts based on severity and likelihood of attack.
By cutting through the noise, security teams can focus on real threats, not just data.
2. Enhancing Incident Detection and Response
Threat intelligence doesn’t just help prevent attacks—it also improves response times when incidents occur. Integrating intelligence into security tools allows analysts to make faster, more informed decisions.
For example:
- An intrusion detection system (IDS) flags a suspicious IP address. If an intelligence feed confirms that the IP is linked to known cybercriminals, analysts can respond immediately.
- A phishing attempt is detected. If similar attacks have been reported in threat feeds, security teams can warn employees before more attempts occur.
- A new vulnerability is found in company software. If there is no record of it being exploited in the wild, it may be lower priority than a vulnerability already used in attacks.
The key is context—knowing who is attacking, what methods they are using, and whether your organization is a target.
3. Tracking Attack Trends to Stay Ahead
Hackers don’t always invent new attacks; many reuse old techniques. By tracking attack trends, organizations can predict which threats they’re most likely to face.
- Ransomware groups tend to exploit the same types of weaknesses. If a particular vulnerability is being used widely in ransomware campaigns, patching it should be a top priority.
- Phishing attacks often target specific industries. If intelligence shows an increase in phishing against banks, financial institutions should take extra precautions.
- Nation-state attackers focus on government and defense sectors. Understanding their tactics helps at-risk organizations strengthen defenses.
By analyzing trends and patterns, businesses can prepare for attacks before they strike.
4. Making Intelligence Work: Real-Time Integration
Threat intelligence is most effective when it’s part of daily security operations, not just stored in a database. Organizations should:
- Integrate intelligence with SIEM platforms to enrich alerts with external data.
- Use automation to apply threat feeds to firewall rules and intrusion detection systems.
- Train security teams to interpret intelligence and act on it effectively.
When intelligence is part of security workflows, it becomes a proactive defense tool rather than just another source of data.
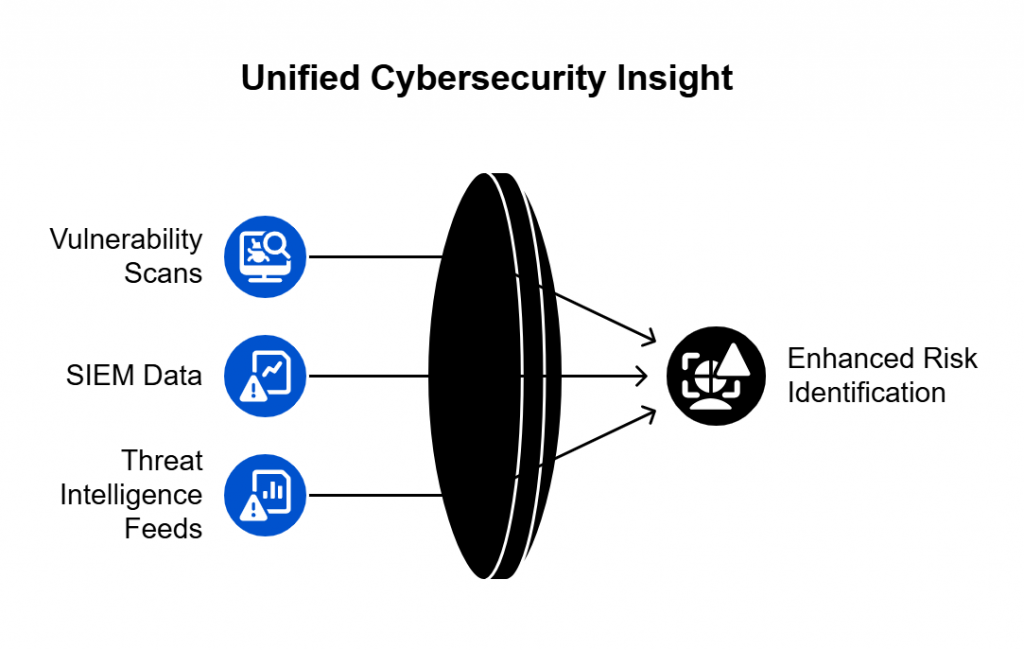
Integrating Vulnerability Scans, SIEM Data, and Threat Feeds for Better Risk Identification
Cyber threats don’t exist in isolation. A single piece of intelligence—whether it’s a vulnerability report, a security alert, or an indicator of compromise—rarely tells the full story. To effectively quantify cyber risks, organizations must combine multiple data sources to gain a holistic view of their security posture.
By integrating vulnerability scans, SIEM (Security Information and Event Management) data, and threat intelligence feeds, security teams can detect threats faster, prioritize risks more effectively, and improve overall defense strategies.
1. Why Integration Matters
Many security tools operate in silos, each generating alerts and reports independently. This leads to fragmented visibility, where teams see parts of the threat landscape but not the full picture. Without integration, organizations face major challenges:
- Too many alerts with no clear priority: Security teams may receive thousands of alerts daily but struggle to identify which ones require immediate action.
- Delayed response to threats: If threat intelligence and security logs are not correlated, teams may overlook signs of an attack until it’s too late.
- Inefficient patch management: Without combining vulnerability data with real-world threat intelligence, teams may waste time fixing low-risk issues while critical exploits remain open.
Bringing these data sources together improves decision-making and helps teams focus on the most dangerous threats first.
2. Combining Vulnerability Scans with Threat Intelligence
Vulnerability scanners (e.g., Nessus, Qualys, Rapid7) are essential for identifying weaknesses in IT systems. However, they often lack context on which vulnerabilities are actively being exploited by attackers.
To improve risk assessment:
- Enrich vulnerability data with threat intelligence feeds. If a vulnerability has known exploits in the wild, it should be prioritized for remediation.
- Use real-time exploit tracking. Some vulnerabilities may be theoretical risks but not yet actively targeted by cybercriminals. If a scanner flags an issue but intelligence feeds show no active exploits, it might be lower priority.
- Correlate with attack trends. If threat reports show that ransomware groups are using a specific vulnerability, patching it should be a top priority.
By combining vulnerability scans with external intelligence, security teams can prioritize patches based on real-world risks, not just theoretical severity scores.
3. Using SIEM Data to Detect Threats in Real-Time
SIEM platforms (e.g., Splunk, IBM QRadar, Microsoft Sentinel) collect and analyze logs from across an organization’s network. They can detect suspicious activity but often produce a high volume of alerts, making it difficult to separate true threats from routine system behavior.
To enhance threat detection:
- Integrate SIEM logs with threat intelligence feeds. If a SIEM detects failed login attempts from an IP address that appears in threat feeds, it should trigger an immediate investigation.
- Correlate SIEM alerts with vulnerability data. If an endpoint is being probed for a known unpatched vulnerability, this is a strong indicator of an attack in progress.
- Automate threat scoring. By combining SIEM data, vulnerability scans, and threat feeds, security teams can assign risk scores to alerts and focus on the highest-priority incidents.
When SIEM data is enriched with external intelligence and internal vulnerability assessments, organizations can detect threats earlier and respond faster.
4. Automating Risk Prioritization with Security Orchestration
Manually analyzing thousands of security events is impossible. Security teams need automation and orchestration tools (e.g., Cortex XSOAR, Anomali, or Splunk Phantom) to make integration seamless.
Key automation strategies include:
- Automated enrichment: When a SIEM alert is triggered, an orchestration tool can automatically pull data from vulnerability scans and threat feeds to provide instant context.
- Dynamic firewall updates: If threat intelligence identifies a malicious IP address, security tools can automatically block it before an attack occurs.
- Incident response workflows: If a new exploit is detected, orchestration tools can trigger automated patching or security policy updates without manual intervention.
By automating threat correlation, security teams can reduce response times, eliminate false positives, and stay ahead of attackers.
5. Improving Risk Identification with a Unified Security Approach
To effectively quantify and manage cyber risks, organizations need to break down security silos and create a centralized risk identification system. This requires:
- A unified dashboard that brings together vulnerability data, SIEM logs, and threat intelligence feeds.
- AI and machine learning tools to analyze and predict which threats pose the highest risks.
- A continuous improvement cycle where security teams refine their threat detection processes based on real-world attack data.
Organizations that integrate multiple security data sources will detect threats earlier, respond faster, and reduce overall cyber risk.
Modeling “What-If” Scenarios for Risk Scoring
Even with the best security tools and data integration, organizations still struggle to quantify risk effectively. Security teams often ask: How likely is this vulnerability to be exploited? What would happen if an attacker breached our system? Which risks should we prioritize?
The answer lies in scenario modeling—a proactive approach that simulates potential attacks, assesses their impact, and assigns a risk score to each threat. This method helps organizations move beyond static security assessments and into real-world, impact-driven risk management.
1. What is Scenario Modeling?
Scenario modeling is the process of creating simulated cyberattack situations to predict how they would unfold in an organization’s environment. Instead of reacting to incidents as they occur, security teams can test various attack scenarios in advance and take preventive action.
For example:
- What if a ransomware attack targeted our financial servers?
- What if a hacker exploited an unpatched vulnerability in our web applications?
- What if a phishing attack compromised an executive’s email account?
By modeling these scenarios, organizations can calculate risk scores, identify weaknesses, and prepare defenses before an actual attack occurs.
2. How Risk Scoring Works
Risk scoring assigns a numerical value to threats based on likelihood, impact, and exploitability. It helps prioritize security efforts by focusing on the highest-risk vulnerabilities and attack vectors.
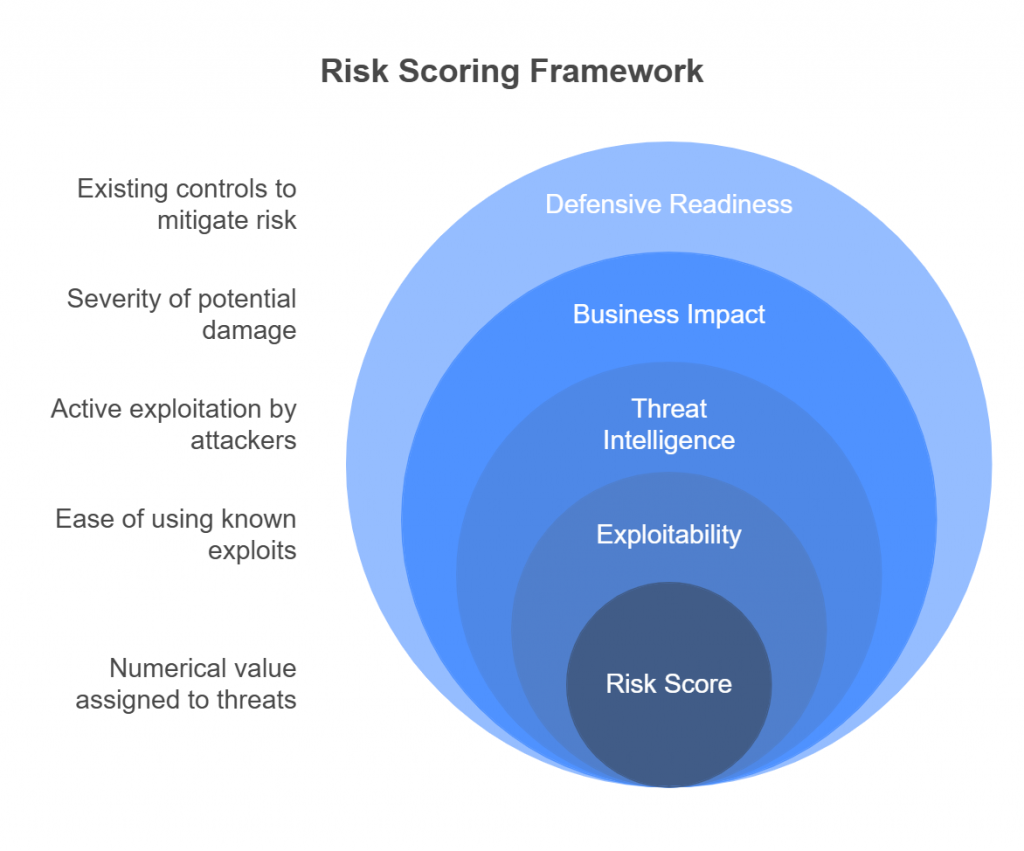
Key factors in risk scoring include:
- Exploitability: Is there a known exploit for this vulnerability? How easy is it to use?
- Threat intelligence data: Are attackers actively exploiting this weakness in the wild?
- Business impact: If this attack succeeds, how severe would the damage be (financial loss, data exposure, operational downtime)?
- Defensive readiness: Does the organization have controls in place to prevent or mitigate this attack?
A high-risk scenario (e.g., an unpatched, actively exploited vulnerability in a critical system) would receive a high score, while a low-impact issue (e.g., a theoretical vulnerability with no active exploits) would receive a lower score.
3. Using “What-If” Simulations to Test Security Posture
Organizations can use attack simulations to test their ability to withstand cyber threats. Popular methods include:
A. Breach and Attack Simulations (BAS)
BAS tools (e.g., SafeBreach, AttackIQ, Cymulate) simulate real-world cyberattacks in a controlled environment. They help answer:
- Can an attacker move laterally within our network?
- How well do our defenses detect and block malicious activity?
- Are critical assets properly segmented and protected?
B. Red Team vs. Blue Team Exercises
- Red teams (ethical hackers) act as attackers, attempting to breach the organization using known tactics.
- Blue teams (defenders) work to detect and stop the attacks, learning in real time how to improve defenses.
These exercises uncover security gaps that traditional testing may miss.
C. Tabletop Exercises
Instead of live testing, tabletop exercises involve cybersecurity teams discussing attack scenarios and response strategies. This helps organizations refine incident response plans without needing full-scale testing.
4. Leveraging AI and Machine Learning for Predictive Risk Modeling
Advancements in AI and machine learning have made it possible to predict cyber risks with greater accuracy. Instead of relying solely on past attack data, AI-driven models can:
- Analyze global attack trends and predict which vulnerabilities are most likely to be exploited.
- Simulate multiple attack paths to identify weak points in an organization’s security posture.
- Provide automated risk scoring based on live threat intelligence and security data.
Machine learning tools can dynamically adjust risk scores as new threats emerge, helping security teams stay ahead of attackers.
5. Applying Risk Modeling to Business Decision-Making
Risk modeling isn’t just for security teams—it also helps executives and decision-makers allocate resources effectively.
- CISOs and security leaders can use risk scores to justify increased security budgets.
- IT teams can prioritize patching and remediation efforts based on real-world risk levels.
- Compliance officers can ensure regulatory requirements are met by addressing high-risk vulnerabilities first.
By connecting cybersecurity risks to business impact, organizations can make data-driven security decisions that improve both protection and efficiency.
Tools and Best Practices for Predictive Analytics in Cybersecurity
The ability to predict cyber threats before they happen is one of the most powerful advantages an organization can have. Predictive analytics, powered by machine learning, big data, and AI-driven insights, helps security teams identify attack patterns, assess vulnerabilities, and prioritize risks with greater accuracy. Instead of reacting to cyber incidents after they occur, organizations can anticipate and mitigate threats before they escalate.
By integrating historical attack data, real-time threat intelligence, and behavioral analytics, predictive models can detect anomalies, forecast emerging threats, and automate responses. This section explores the tools and best practices organizations can use to make predictive cybersecurity a reality.
How Predictive Analytics Works in Cybersecurity
Predictive analytics relies on past and present data to forecast future cyber risks. It analyzes attack trends, security logs, and user behaviors to detect patterns that indicate potential threats.
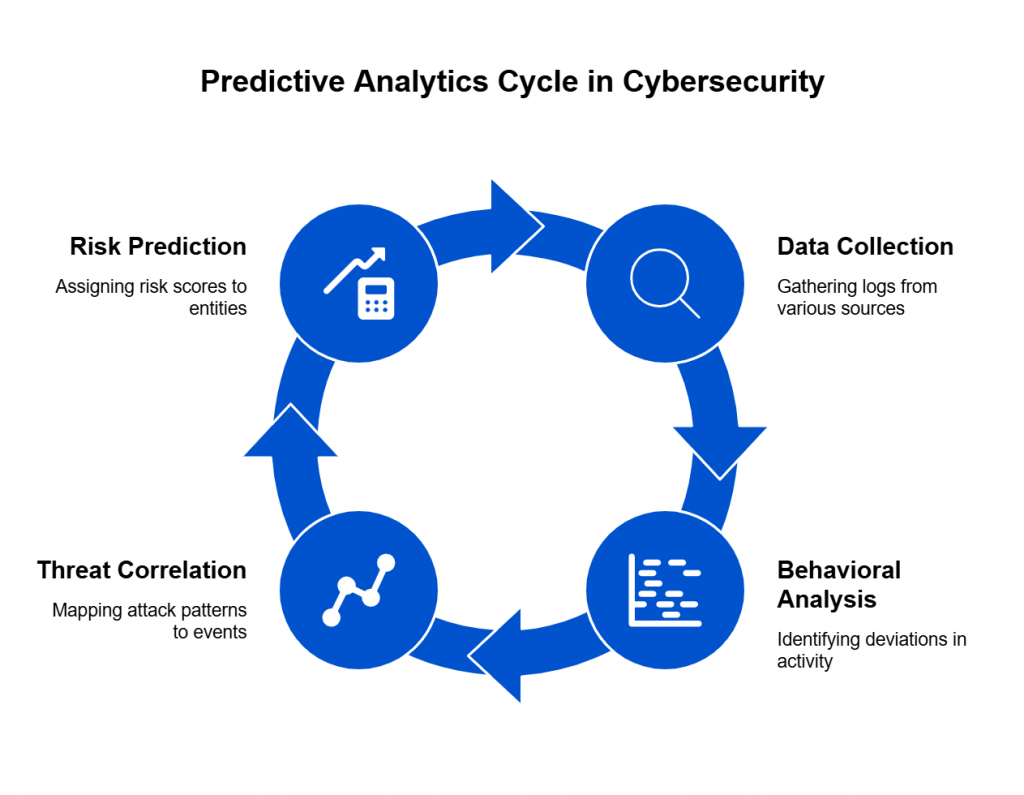
The process involves:
- Data Collection: Gathering logs from SIEM platforms, firewalls, IDS/IPS systems, and threat intelligence feeds.
- Behavioral Analysis: Identifying deviations from normal user and system activity.
- Threat Correlation: Mapping historical attack patterns to current security events.
- Risk Prediction: Assigning risk scores to systems and users based on their likelihood of compromise.
By combining these techniques, organizations can identify threats before they materialize, reducing the impact of cyberattacks.
Key Predictive Analytics Tools for Cybersecurity
Several advanced security tools leverage AI and machine learning to predict and prevent cyber threats. Some of the most effective include:
User and Entity Behavior Analytics (UEBA)
UEBA tools analyze the behavior of users, devices, and applications to detect unusual activity that may indicate an insider threat or external attack.
Popular UEBA tools:
- Splunk UBA – Identifies abnormal user behavior and insider threats.
- Exabeam – Uses machine learning to track deviations in user activity.
- Microsoft Defender for Identity – Detects identity-based threats in real time.
AI-Powered SIEM Solutions
Traditional SIEM platforms generate massive amounts of security data. AI-enhanced SIEM solutions help filter out noise and prioritize real threats.
Popular AI-powered SIEM tools:
- IBM QRadar – Uses AI-driven threat intelligence to detect attack patterns.
- Elastic Security (formerly ELK Stack) – Provides real-time log analysis and anomaly detection.
- Microsoft Sentinel – Integrates machine learning to predict and prevent cyber threats.
Security Orchestration, Automation, and Response (SOAR)
SOAR platforms automate incident response by using AI to analyze threats and trigger automated actions.
Popular SOAR tools:
- Palo Alto Cortex XSOAR – Automates security workflows and threat mitigation.
- Splunk Phantom – Uses AI to respond to security incidents in real time.
- Swimlane – Automates security tasks and orchestrates incident response.
By integrating these predictive analytics tools, organizations can proactively detect threats, reduce response times, and enhance overall cybersecurity posture.
Best Practices for Implementing Predictive Cybersecurity Analytics
To maximize the effectiveness of predictive analytics, organizations should follow these best practices:
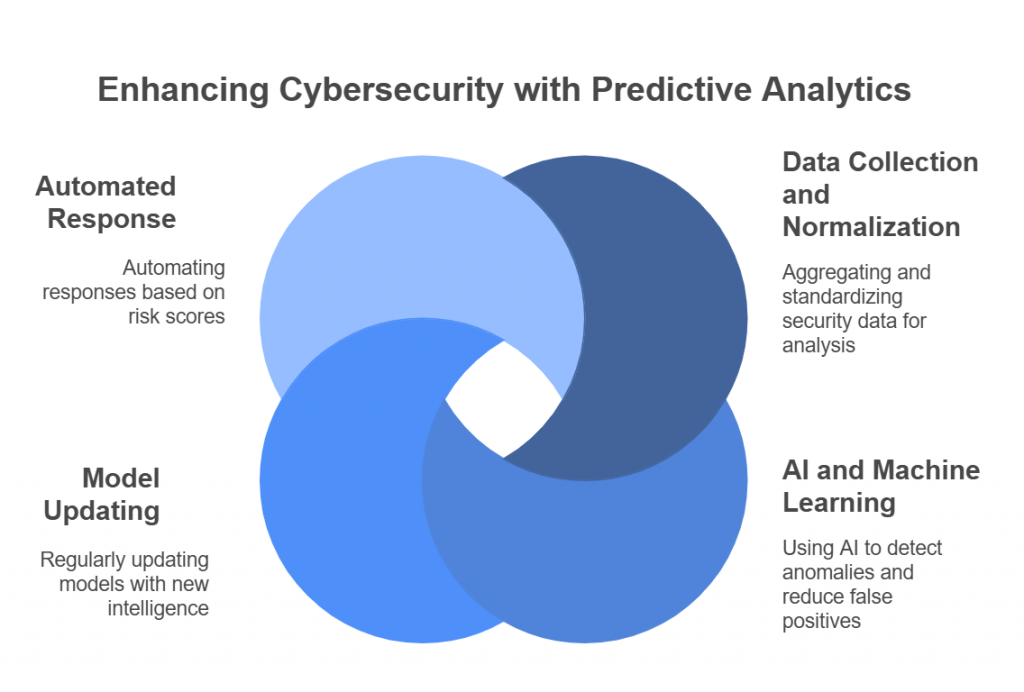
Collect and Normalize Security Data
Predictive models are only as good as the data they analyze. Organizations should:
- Aggregate logs from firewalls, endpoints, cloud services, and security tools.
- Normalize data formats to ensure compatibility across platforms.
- Remove duplicate or irrelevant logs to improve analysis efficiency.
Use AI and Machine Learning to Detect Anomalies
Instead of relying solely on static rules, AI-based systems can:
- Detect small deviations in behavior that traditional security tools might miss.
- Identify zero-day threats by analyzing global attack trends.
- Reduce false positives by learning from past security events.
Continuously Update Predictive Models
Cyber threats evolve constantly, so predictive models must be updated frequently. Security teams should:
- Regularly train AI models with new threat intelligence.
- Integrate real-time global threat feeds to keep predictions relevant.
- Conduct ongoing assessments to fine-tune algorithms.
Automate Incident Response Based on Risk Scores
To reduce response times, organizations can:
- Assign risk scores to security alerts based on predictive analysis.
- Trigger automated defenses for high-risk threats (e.g., blocking malicious IPs or quarantining compromised devices).
- Escalate low-risk anomalies for manual review instead of overwhelming security teams with unnecessary alerts.
Real-World Applications of Predictive Cybersecurity
Several industries have successfully implemented predictive analytics to prevent cyber incidents before they occur:
- Financial Services: Banks use AI-driven fraud detection systems to identify suspicious transactions before they lead to major breaches.
- Healthcare: Hospitals leverage predictive cybersecurity to detect unauthorized access to patient records and prevent ransomware attacks.
- E-commerce: Online retailers use behavioral analytics to flag fraudulent login attempts and prevent account takeovers.
By applying predictive analytics, organizations can identify emerging threats, reduce breach risks, and strengthen security operations.
Conclusion
Cyber threats are evolving at an unprecedented pace, making traditional, reactive security measures increasingly ineffective. Organizations can no longer afford to wait for an attack to happen before taking action. Instead, they must embrace advanced techniques for risk identification, leveraging threat intelligence, predictive analytics, and real-world attack simulations to stay ahead of adversaries.
By integrating vulnerability scans, SIEM data, and threat intelligence feeds, businesses can gain a holistic view of their risk landscape. Modeling “what-if” attack scenarios enables security teams to predict and prepare for the most likely threats, ensuring that the most critical risks are prioritized. Meanwhile, AI-driven predictive analytics is transforming cybersecurity by detecting anomalies, assigning risk scores, and automating defenses before an attack escalates.
However, technology alone is not enough. Cyber risk quantification requires a shift in mindset—from reactive security postures to proactive, data-driven decision-making. Organizations must continuously refine their risk models, update threat intelligence, and enhance security automation to keep pace with evolving threats.
The future of cybersecurity belongs to those who measure, predict, and mitigate risks before they turn into breaches. By embracing these advanced techniques, businesses can strengthen their security posture, protect their digital assets, and build long-term resilience against the ever-changing threat landscape.
