Introduction: The Audit That Changed Everything
Alex had been at the fintech startup for just under a year when the audit notice landed in his inbox.
He wasn’t worried—at first. The engineering team was solid. The infrastructure was clean. Everything was built with intention: containers spun up and down gracefully, deploys were fast and observable, logs were rich and structured. Surely compliance would be a formality.
Then came the ask: “We need evidence of quarterly access reviews.”
No problem, Alex thought. Until he looked.
The access review spreadsheet? Locked. Owner unknown. The shared folder? Gone. Slack thread? Buried. Sarah, the compliance manager, would know—except Sarah had left six months ago.
Two days later, after pinging five teams, reviving archived threads, and begging IT for forensic file recovery, the truth hit harder than any breach report:
The company had engineered its product beautifully.
But it had never architected its compliance.
The story might sound dramatic. But if you’ve worked in security, risk, or compliance, you’ve lived a version of it. Maybe you are Alex.
And the numbers back it up:
- 57% of organizations cite fragmented systems as the top barrier to continuous compliance (ISACA, 2023).
- 74% of companies view compliance as a burden. (Hyperproof, 2022).
- The average cost of non-compliance? A staggering $5.87 million (Ponemon Institute/Globalscape, 2023).
Compliance isn’t failing because teams don’t care.
It’s failing because the systems that hold our controls, evidence, and risk data don’t speak to each other.
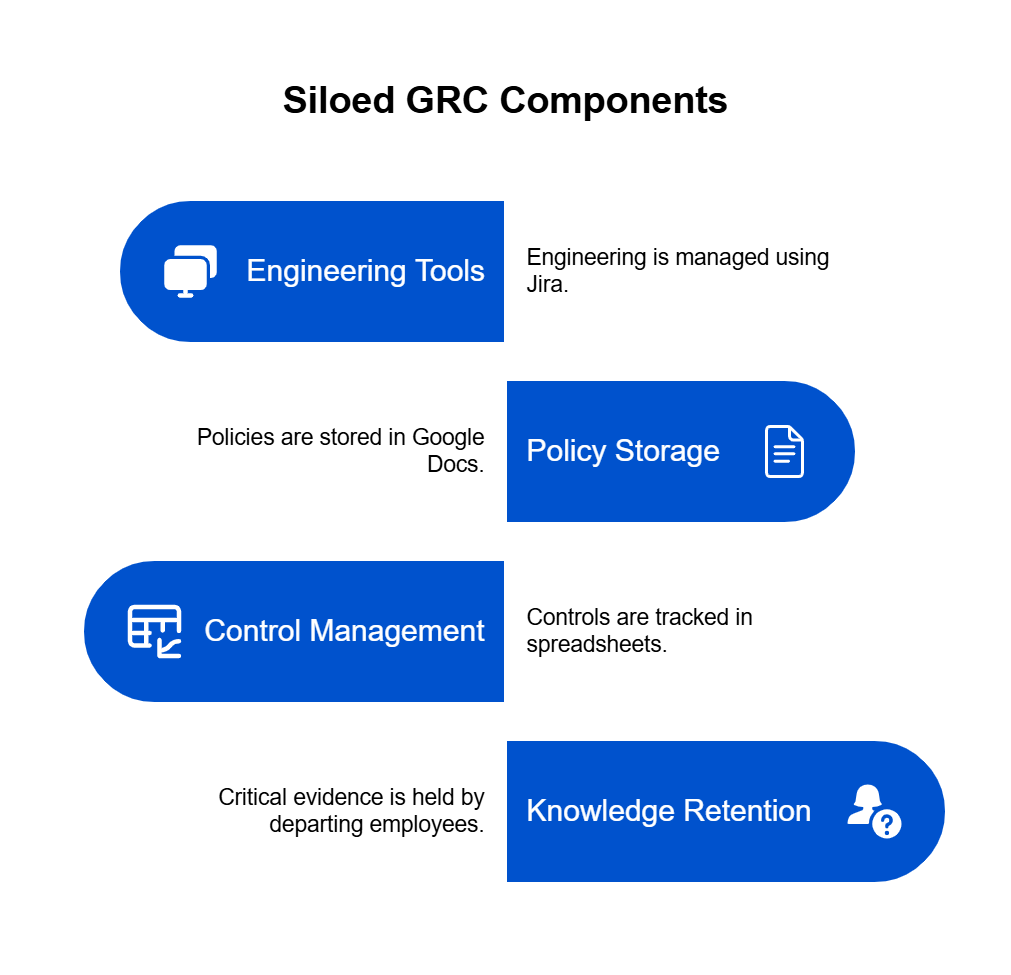
Instead of a unified GRC system, we have silos:
✔️ Engineering in Jira
✔️ Policies in Google Docs
✔️ Controls in spreadsheets
✔️ Evidence in someone’s brain (who just left the company)
Before you can automate compliance, you have to design it. You have to map the flows, build the language, and define how teams connect.
Because tools don’t solve chaos—they scale it.
Why Compliance Breaks (Even When Everyone Means Well)
Nobody sets out to build a broken compliance program.
It just… happens.
One team tracks risks in a spreadsheet. Another stores evidence in a shared drive. Someone builds a homegrown tool. Then another team buys a vendor product. Fast forward six months, and no one can find the latest access review, and nobody knows what “critical” means anymore.
The result?
A system that feels organized—until it’s time for an audit.
Meanwhile, engineering has CI/CD pipelines, monitoring, clean logs, and automation everywhere. They can push code five times a day. But your compliance team is still waiting on screenshots, asking “who owns this control,” and chasing last year’s risk register.
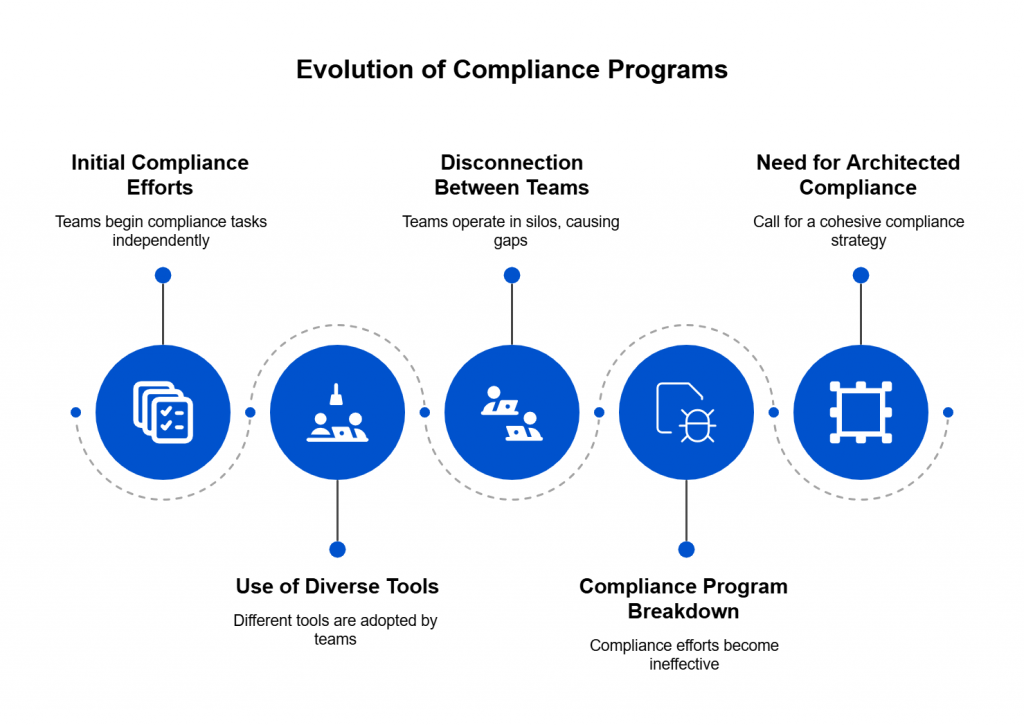
The speed of your business doesn’t match the speed of your compliance.
That’s not just frustrating. It’s dangerous.
Because while teams are working hard in their corners, the lack of connection between them creates blind spots. And in those blind spots?
Breaches. Missed controls. Failed audits.
Not because people failed.
Because the system wasn’t built to work together.
So before you automate compliance—or scale it—you need to architect it.
Think of it like infrastructure-as-code, but for GRC.
Before the deployment comes the design.
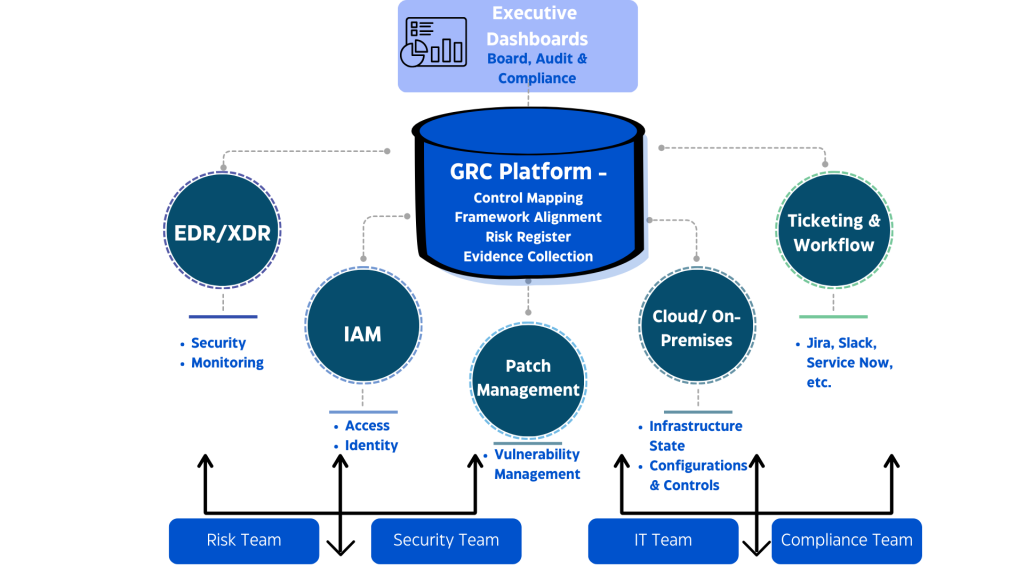
The Integrations That Actually Matter
You don’t need more tools.
You need the right ones—talking to each other.
Compliance doesn’t break because a control fails. It breaks because systems don’t speak. Teams don’t share context. Data doesn’t move.
That’s why integrations aren’t just “nice-to-have.” They’re the nervous system of a modern GRC stack.
Here are the integrations that make the biggest difference—day one.
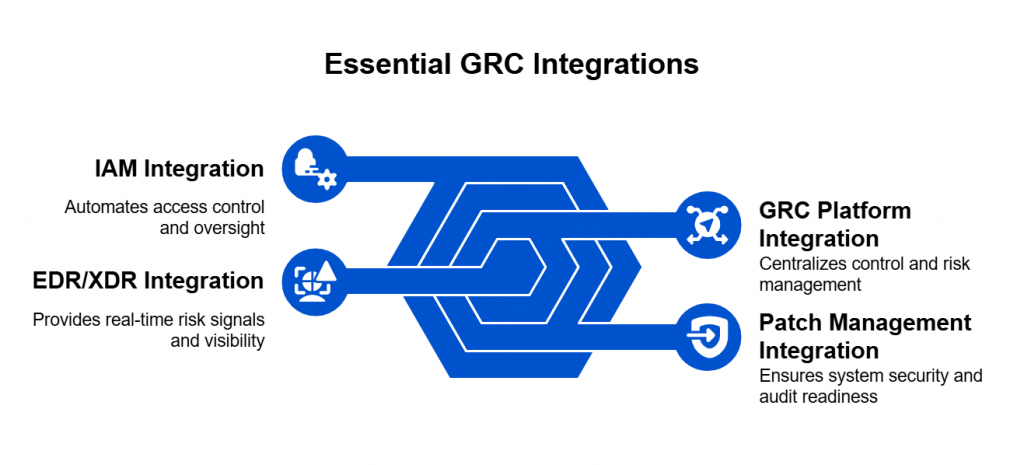
1. EDR/XDR: Your Early Warning System
Your endpoints and networks are where the action happens—and where the trouble starts.
When you integrate your EDR/XDR with your GRC platform:
- Security incidents show up as real-time risk signals
- Evidence collects itself (no more Slack messages begging for screenshots)
- You can prove, not just promise, that you’re monitoring threats
This isn’t just technical visibility. It’s compliance with eyes open.
2. GRC Platform: Your Control Center
Think of your GRC tool as mission control. But without integrations, it’s just a dashboard full of dead dials.
Connected to the right systems, a GRC platform can:
- Auto-map technical controls to frameworks like ISO 27001, NIST, SOC 2
- Track risk posture in real time
- Pull live evidence instead of outdated docs
With integrations, your GRC isn’t a burden. It’s a source of truth.
3. Patch Management: Your First Line of Defense
Unpatched systems are low-effort targets for attackers—and top-tier audit failures.
Integrated patching gives you:
- Visibility into what’s been fixed (and what hasn’t)
- Auto-alerts for missing critical patches
- Evidence logs ready for audits
It turns patching from a fire drill into a measurable control.
4. IAM: Your Who-Can-Do-What Engine
Access control is a compliance staple. But when IAM lives in a silo, mistakes slip through.
Integrating IAM means:
- Automated tracking of who has access to what
- Alerting on privilege creep
- Evidence tied to actual roles and activity—not assumptions
This turns identity from a static checklist into dynamic control assurance.
These integrations don’t just plug holes.
They create flow—so risk becomes data, data becomes evidence, and evidence tells a real story.
The right tools, wired the right way, give you a GRC system that works as fast as your business does.
Why Real-Time Beats Manual (Every Time)
Manual compliance is like chasing shadows. You think you’ve captured the risk, logged the evidence, checked the box—until the environment changes, again. And it always does.
That’s the problem.
You can’t secure what you can’t see in time. And manual compliance processes are always a few steps behind reality.
Let’s say your team pushes a permissions change to a production system—someone gets elevated access temporarily. That access is revoked two hours later. But your quarterly access review won’t catch it. Your audit trail won’t show it. And if that access was misused? You’d never know.
That’s the gap between documented compliance and actual security. And it’s growing wider in every fast-moving organization.
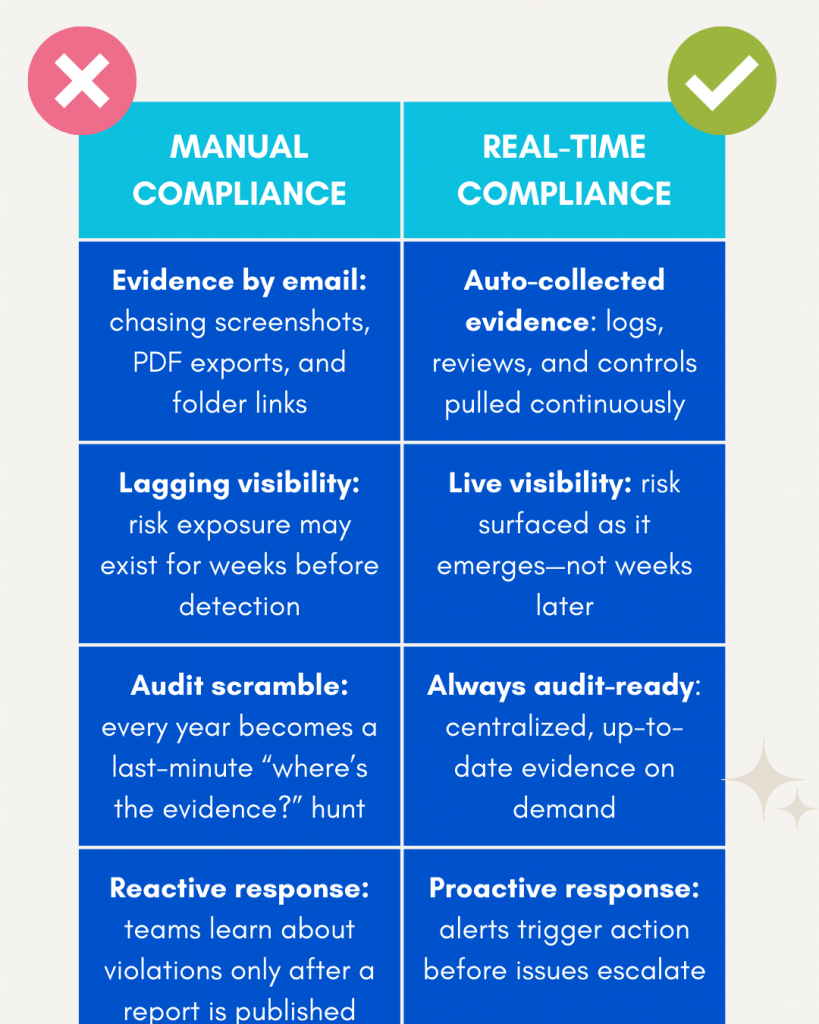
Real-Time Isn’t Just Faster—It’s Smarter
Real-time systems don’t just reduce effort. They change the quality of your compliance posture.
Instead of stale documentation, you have living data. Instead of vague control ownership, you have audit trails. Instead of quarterly risk reviews, you have daily insights.
Your reports become reliable. Your audits become easier. Your business decisions become more informed.
And when a regulator, auditor, or board member asks, “Are we secure?”
You can say, confidently: “Let me show you.”
The Hidden Cost of Lag
Organizations running on manual processes don’t just suffer inefficiency—they expose themselves to actual risk:
- Missed SLAs on vulnerability remediation
- Data retention violations due to undocumented access
- Control drift between what’s defined on paper and what’s active in production
- Fines and penalties for failure to demonstrate ongoing compliance
The financial risk is very real. So is the reputational damage.
In fact, according to the Ponemon Institute, companies with no real-time compliance visibility suffer breach costs 40% higher on average than those with automated, integrated systems.
What Real-Time Requires
To move from manual to real-time compliance, you don’t need to rip and replace your stack. But you do need:
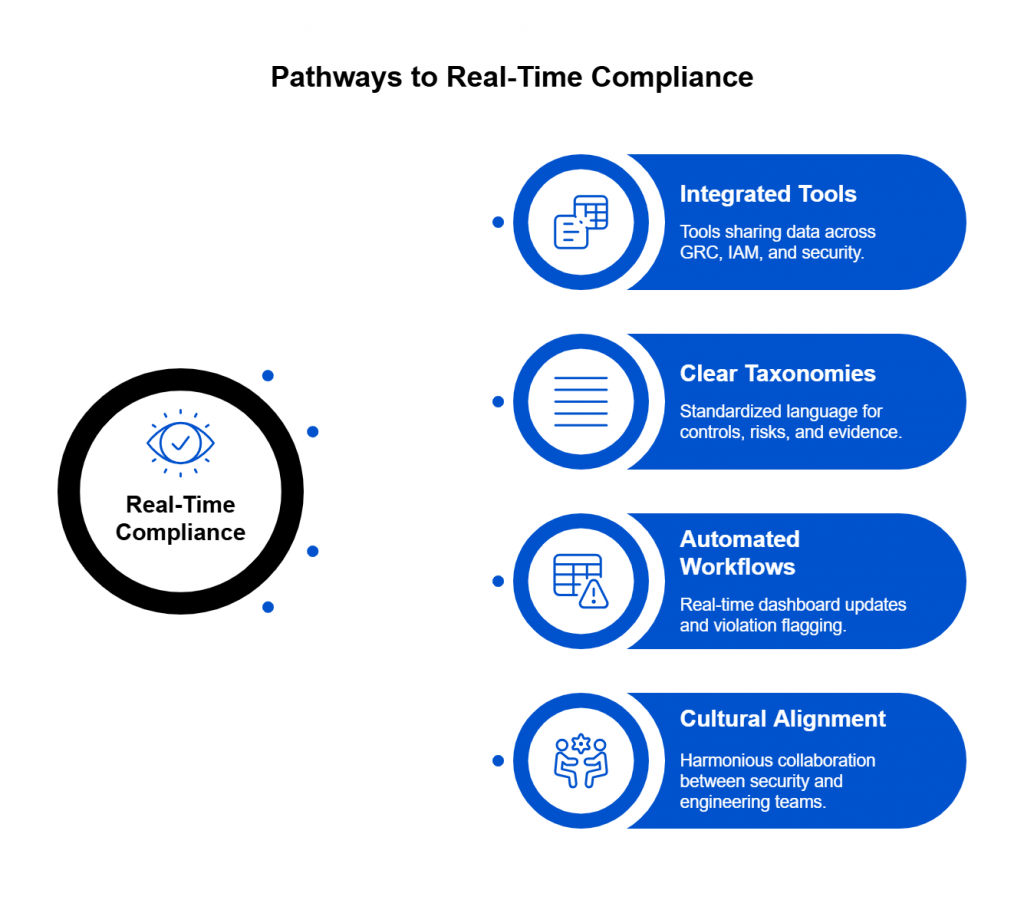
- Integrated tools that share data across GRC, IAM, patching, and security systems
- Clear taxonomies so controls, risks, and evidence speak the same language
- Automated workflows that update dashboards and flag violations as they happen
- Cultural alignment between security, risk, and engineering teams
The tools already exist. The data already flows. The only thing missing in most organizations?
Architecture. Intent. Integration.
Where Automation Actually Delivers ROI
Hint: It’s not everywhere.
Automation is a powerful tool—but only if it’s pointed in the right direction. If your processes are broken, automation just makes the chaos move faster.
That’s why you don’t start with tools. You start with architecture—then you automate with intent.
But once you’ve got the right foundation in place?
Automation becomes a force multiplier.
Here’s where it pays off—fast:
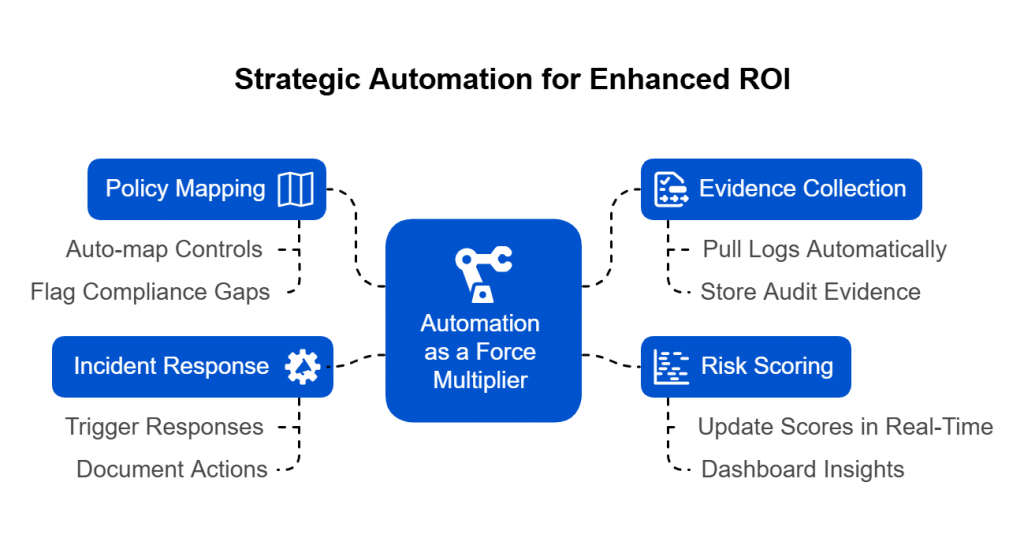
1. Policy Mapping That Updates Itself
Imagine every time a control changes, it auto-maps to your frameworks—NIST, ISO, SOC 2—without anyone updating a spreadsheet.
When your systems are integrated, automation can:
- Map technical controls to multiple frameworks
- Flag gaps in compliance coverage
- Update policy status as systems change
This turns documentation into a dynamic, always-current asset.
2. Continuous Evidence Collection
No more screenshot scavenger hunts. No more “Can you export that log real quick?”
Integrated systems can automatically:
- Pull logs, access records, and test results
- Time-stamp and store them as audit evidence
- Match them to the relevant control or risk
Instead of manual uploads and folders, you get a live audit trail—ready when you need it.
3. Automated Risk Scoring
What’s your riskiest control today? Yesterday? Last week?
With automation:
- Alerts, findings, and incidents feed directly into your risk model
- Scores update in real time based on likelihood and impact
- You get dashboards that show shifting risk—not static risk
This helps security, compliance, and leadership prioritize with data—not instinct.
4. Incident Response Workflows
An incident happens. Your system reacts.
With automation:
- A detection in XDR triggers a ticket in Jira
- IAM flags the account for review
- GRC logs the event, updates the risk register, and notifies stakeholders
- Evidence is auto-tagged and stored
The response isn’t just faster—it’s documented, repeatable, and audit-ready.
Where Automation Fails (If You’re Not Careful)
Let’s be honest. Automation isn’t magic.
If your control taxonomy is inconsistent, if teams don’t speak the same language, or if your evidence lives in silos—automation will make the mess worse.
That’s why you must design before you automate.
Think of it like DevOps. You wouldn’t deploy to production without version control, pipelines, and rollback strategies. Same goes for GRC.
Architect first. Then automate with purpose.
The ROI Is Clear
Organizations with integrated and automated GRC processes see:
- 30–50% reduction in audit prep time
- Fewer compliance gaps and late findings
- Improved cross-team alignment between security, compliance, and engineering
- Faster response to incidents and regulatory inquiries
That’s not just operational efficiency. That’s a return on trust, time, and risk reduction.
Deploying Integrated GRC: Best Practices That Actually Work
You’ve mapped your risks. You’ve picked your tools. You’re ready to connect the dots.
But let’s be real: deploying an integrated GRC ecosystem isn’t a flip-the-switch project. It’s closer to a system refactor—incremental, intentional, and collaborative.
Here’s how to approach it without burning out your team or breaking your business.
1. Map Your Information Ecosystem First
Before buying anything, draw a map. Seriously.
Sketch out where your data lives today:
- Where do access reviews start?
- Where are findings logged?
- Where does risk data stall?
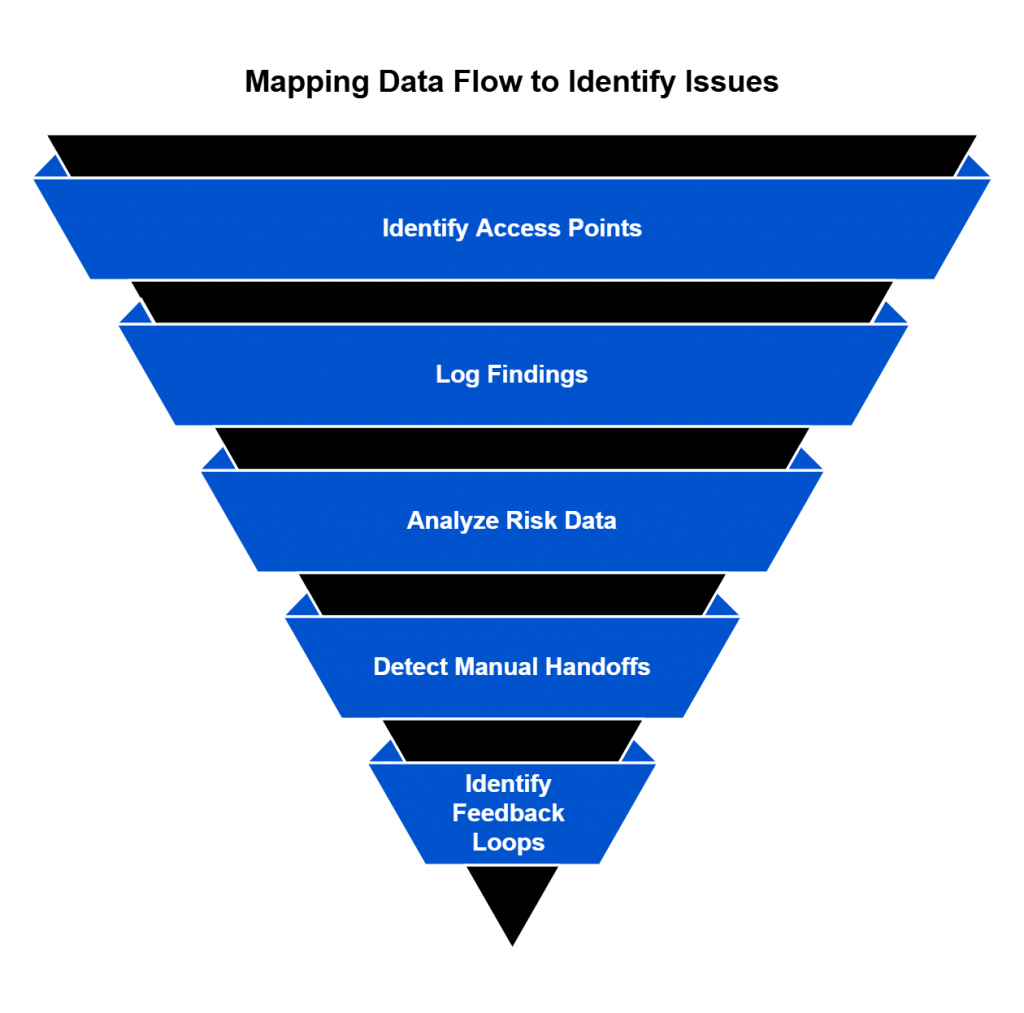
Identify:
- Manual handoffs
- Broken feedback loops
- Silos with no clear owners
This is your compliance flowchart. It doesn’t need to be pretty. It just needs to be honest.
It will quickly show you where the pain is—and where integration has the most impact.
2. Establish a Unified Data Model
If “critical” means one thing to security and something else to compliance, you’re not integrated. You’re just adjacent.
You need:
- A shared taxonomy for risks, controls, findings, and evidence
- Standard labels (e.g., “High,” “Medium,” “Low”) across systems
- Clear relationships:
- Controls mitigate risks
- Evidence supports controls
- Findings indicate control failures
Think of this as GRC schema design. Without it, automation breaks. With it, everything speaks the same language.
3. Define Team Interfaces Like APIs
Engineering has clear interfaces. Your GRC program should too.
Ask:
- What information does security provide to GRC?
- What does GRC need from engineering?
- How do compliance teams pull from IAM, XDR, patching tools?
Document these like you would API endpoints:
- Input → Format → Owner → Frequency
These human-system interfaces are what you’ll automate later. But even before that, they create clarity, consistency, and shared expectations.
4. Start with One Use Case and Scale
Don’t try to integrate everything at once. Pick a high-impact area—like access reviews or vulnerability remediation—and connect just that.
Prove it works.
Get buy-in.
Then expand.
Start small, move fast, and scale what succeeds.
5. Choose Tools That Speak API
Integration is only as good as your tools’ ability to communicate.
Prioritize:
- Open APIs
- Webhooks
- Native integrations with your existing stack
- Community support (because you’ll need it)
A beautiful GRC platform is useless if it can’t connect to the systems that matter most.
6. Build for Change, Not Just Today
Compliance requirements evolve. So do your tools, teams, and threats.
Design your system to adapt:
- Use flexible data structures
- Avoid hardcoding workflows
- Document everything so new teammates don’t start at zero
What you want is compliance agility—not just compliance coverage.
Bonus: Treat GRC Like a Product
Have a backlog. Assign ownership. Collect feedback. Ship improvements.
The best GRC programs are built like internal products—because they support the entire organization.
With these practices, you’re not just checking boxes. You’re building a system that can evolve with your business—and keep it safe along the way.
Rethink Compliance. Architect for the Future. Power It with Spog.ai.
The age of fragmented spreadsheets and last-minute evidence hunts is over.
The stakes are too high. The pace of change is too fast. The cost of failure is too real.
To protect your business—and prove you’re doing it—you need more than policies.
You need a system. A language. A flow.
Spog.ai is built for this.
It’s not just another GRC tool. It’s a platform that connects your stack, understands your risk, and gives you real-time, ROI-driven visibility into your compliance posture.
✅ Automate evidence collection
✅ Prioritize remediation based on actual risk
✅ Align your controls, teams, and audits—all in one place
Compliance isn’t a box to check.
It’s a business function.
A trust signal.
A strategic differentiator.
And it starts with architecture.