The truth is that VM tools alone are not enough. They generate large amounts of data but lack the strategic insights needed to improve security. Security teams often feel overwhelmed by thousands of alerts. They struggle to prioritize, remediate efficiently, and align security efforts with business and compliance goals.
- Are you fixing the right vulnerabilities or just the ones your tool highlights?
- Are you tracking the right metrics to measure risk reduction?
- Are compliance gaps being ignored while security teams focus on low-impact issues?
An unpatched critical vulnerability is not the only risk. A vulnerability management program that lacks key insights can be just as dangerous. To improve security, CISOs and cybersecurity teams must go beyond tools and start tracking the right vulnerability management metrics.
Below are the 10 critical metrics every organization should monitor.
1. Asset coverage
Asset coverage is one of the most fundamental metrics, yet it is often incomplete. It measures the percentage of organizational assets that are included in vulnerability scans. If certain systems, cloud workloads, or shadow IT assets are left unscanned, they create security blind spots that attackers can exploit.
This metric is calculated by dividing the number of scanned assets by the total known assets in the organization. For example, if an organization has 10,000 devices but only 8,000 are regularly scanned, their asset coverage is just 80%, leaving 2,000 devices vulnerable and unmanaged.
2. Vulnerability Volume
Beyond just knowing how many assets are scanned, organizations must also track vulnerability volume—the total number of vulnerabilities detected across all assets. While this number gives an overall view of security exposure, it needs context.
A high vulnerability count does not necessarily mean high risk; it may just reflect a broader scanning scope. Security teams often compare current vulnerability volume to historical trends to determine whether security measures are improving or if new risks are emerging.
For example, if last quarter’s scans detected 50,000 vulnerabilities and this quarter shows 70,000, it could indicate either a growing attack surface or better detection capabilities.
3. Critical Vulnerabilities
Not all vulnerabilities carry the same level of risk, which is why tracking critical vulnerabilities is essential. These are vulnerabilities that are either actively exploited, have a high CVSS score, or affect critical business systems.
This metric is calculated by filtering vulnerabilities that meet specific risk criteria, such as a CVSS score of 9.0+, those with known exploits, or those affecting assets with high business value.
For instance, if a company has 10,000 vulnerabilities, but 300 of them are classified as critical and directly impact customer-facing applications, those 300 must be prioritized over lower-risk issues.
4. Time to Remediate (TTR)
Time to remediate (TTR) measures how quickly vulnerabilities are patched after they are identified. Delays in remediation increase the risk of exploitation, especially when dealing with zero-day vulnerabilities or actively exploited flaws.
TTR is calculated by taking the average number of days between the detection of a vulnerability and its remediation.
If an organization takes an average of 30 days to patch high-risk vulnerabilities while attackers exploit them in 7 days, there is a significant security gap. Reducing TTR ensures vulnerabilities are addressed before they can be weaponized.
5. Open vs. Closed Vulnerabilities
Knowing how many vulnerabilities exist is one thing, but tracking how many are actually being fixed is another. Open vs. closed vulnerabilities is a metric that compares the number of vulnerabilities that remain unresolved to those that have been successfully remediated.
A high number of open vulnerabilities can indicate slow patching, resource constraints, or poor remediation workflows.
Suppose a company identifies 20,000 vulnerabilities in a quarter but only resolves 8,000. That means 12,000 vulnerabilities remain open, representing a growing backlog that could lead to serious security risks.
6. Recurrent Vulnerabilities
Even worse, some vulnerabilities resurface even after they are patched, which is why tracking recurrent vulnerabilities is critical. This metric helps identify weaknesses in patching processes, misconfigurations, or overlooked dependencies.
It is calculated by tracking how often a previously patched vulnerability reappears in subsequent scans.
For instance, if a vulnerability affecting a key application was marked as resolved but keeps appearing due to a misconfigured patching system, it signals a need for process improvement rather than just reapplying the patch.
7. Patch Compliance
Patch compliance ensures that security teams are applying patches within the recommended timelines. Many organizations have internal policies or regulatory requirements that specify how quickly high-risk vulnerabilities should be patched—typically within 30 days.
Patch compliance is measured by the percentage of vulnerabilities that are patched within the required timeframe.
If a company has 500 critical vulnerabilities and only 300 are patched within the required SLA, their compliance rate is just 60%, which could lead to audit failures or regulatory penalties.
8. Risk Scores
To add more intelligence to prioritization, organizations should track risk scores instead of relying purely on severity ratings. Risk scores combine technical severity, exploitability, and business impact to provide a more accurate view of what should be addressed first.
Many modern security platforms use machine learning models or threat intelligence feeds to dynamically adjust risk scores based on real-world attack data. For example, a vulnerability with a CVSS score of 7.5 might be deprioritized if it has no known exploits, while another vulnerability rated 6.5 but actively targeted in the wild would receive a higher priority.
9. SLA Compliance
If SLAs dictate that critical vulnerabilities must be fixed within 15 days, but only 50% of them are addressed in time, it suggests bottlenecks in the remediation process. Regularly tracking SLA compliance helps organizations avoid compliance failures and prevent security incidents caused by overdue vulnerabilities.
SLA compliance is another key metric that ensures vulnerabilities are remediated within agreed timeframes. Security teams often work under SLAs that define how quickly different categories of vulnerabilities must be resolved.
10. Compliance Metrics
Finally, compliance metrics measure how well the organization adheres to security frameworks such as ISO 27001, PCI DSS, and NIST 800-53. Many industries have specific regulations that require organizations to maintain a certain level of security hygiene, including vulnerability management.
This metric is often evaluated through automated compliance reports, audit logs, and policy adherence tracking. If an organization operates in finance or healthcare and fails to meet PCI DSS or HIPAA security standards, it could face heavy fines and reputational damage.
| Metric | Description | Why It Matters |
| Asset Coverage | Tracks the percentage of organizational assets included in scans (e.g., endpoints, servers, applications). | Ensures that no asset is left unmonitored, eliminating blind spots that attackers could exploit. |
| Vulnerability Volume | Measures the total number of vulnerabilities detected in the environment. | Provides an understanding of the overall risk landscape and helps allocate resources efficiently. |
| Critical Vulnerabilities | Identifies vulnerabilities classified as high-risk based on severity and exploitability. | Ensures that high-risk vulnerabilities are prioritized and remediated to reduce the likelihood of critical breaches. |
| Time-to-Remediate (TTR) | Tracks the average time it takes to remediate vulnerabilities after detection. | Reduces exposure time by ensuring timely responses to identified risks. |
| Open vs. Closed Vulnerabilities | Compares the number of unresolved vulnerabilities to those that have been remediated. | Helps monitor progress, identify bottlenecks, and drive accountability in remediation efforts. |
| Recurrent Vulnerabilities | Tracks vulnerabilities that reappear after being resolved. | Highlights systemic issues like poor patching processes or configuration drift, ensuring long-term fixes. |
| Patch Compliance | Measures the percentage of systems with patches successfully applied within defined timelines. | Ensures that critical patches are deployed on time, reducing attack surface and preventing exploitation. |
| Risk Scores | Assigns a risk score to each vulnerability based on severity, exploitability, and business impact. | Helps prioritize vulnerabilities that pose the highest risk to organizational operations and compliance. |
| SLA Compliance | Tracks adherence to service-level agreements (SLAs) for vulnerability remediation timelines. | Ensures that critical vulnerabilities are resolved within agreed timeframes, reducing the risk of prolonged exposure. |
| Compliance Metrics | Measures adherence to regulatory and internal security frameworks (e.g., ISO 27001, PCI DSS). | Demonstrates regulatory compliance, reduces audit risks, and ensures alignment with industry standards. |
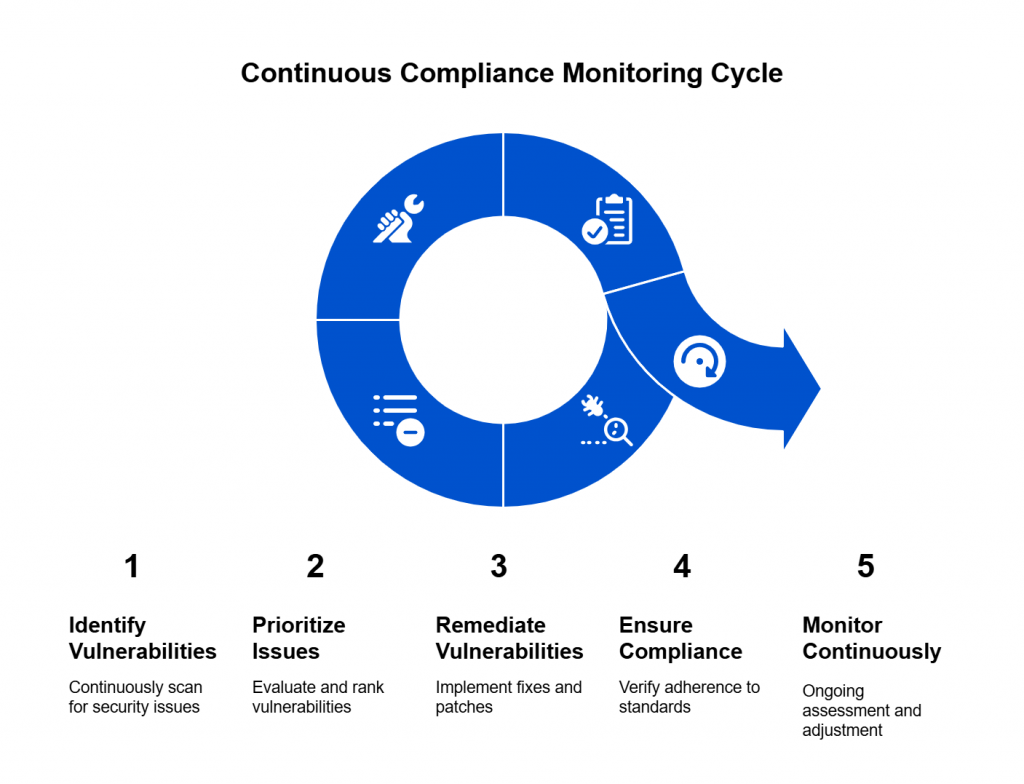
Tracking Metrics with Continuous Compliance Monitoring
Let’s be honest—most organizations are drowning in vulnerabilities. Security teams run scans, find thousands of issues, and then scramble to patch what they can. But despite all this effort, attackers still find their way in. Why? Because vulnerability management tools alone don’t cut it. They tell you what’s wrong but don’t help you fix what actually matters.
This is where Continuous Compliance Monitoring (CCM) changes the game. CCM doesn’t just scan and report vulnerabilities—it helps security teams prioritize, remediate, and stay compliant in real time. Instead of playing catch-up, organizations using CCM get ahead of risks before they turn into breaches.
Security is About More Than Just Scanning
Think about your organization’s assets—cloud workloads, internal servers, third-party applications, and shadow IT that nobody admits to using. Traditional VM tools only scan what they know about. But what about the unknown? If security teams don’t have a complete picture of their digital environment, they’re leaving gaps attackers can exploit.
CCM fixes this visibility problem. Instead of waiting for someone to manually input an asset list, it continuously maps everything—on-prem, cloud, hybrid environments, and even third-party dependencies. If a new system pops up that wasn’t there last week? CCM flags it immediately so it can be monitored before it becomes a security liability.
Fixing the Right Vulnerabilities, Not Just the Loudest Ones
Not all vulnerabilities are created equal, but you wouldn’t know that from looking at a CVSS score alone. Security teams often get caught up in chasing high-severity issues that aren’t actually exploitable while missing medium-severity ones that attackers are actively using.
CCM doesn’t just rely on static severity scores—it prioritizes vulnerabilities based on real-world risk. It asks the questions that actually matter:
- Is this vulnerability being actively exploited in the wild?
- Does it affect a business-critical application?
- Is it required to meet compliance standards?
For example, imagine you have two vulnerabilities:
🔹 One is rated CVSS 9.0 but sits on an internal, non-critical system.
🔹 The other is CVSS 6.5 but affects a customer-facing app and has an active exploit kit available.
Most VM tools will tell you to fix the 9.0 vulnerability first, even though attackers are more likely to go after the 6.5 issue. CCM corrects this flawed logic by combining threat intelligence, compliance impact, and business context to make smarter prioritization decisions.
Staying Compliant Without the Last-Minute Panic
Ask any security team how much they love audits, and you’ll probably get an eye roll. Compliance isn’t just about checking boxes—it’s about staying ahead of security risks before they put your organization at risk of fines or legal trouble.
Traditional VM tools don’t do compliance tracking well. They tell you about vulnerabilities, but they don’t map them to compliance frameworks like ISO 27001, PCI DSS, or NIST. That means security teams often find themselves scrambling before audits, manually piecing together reports to prove they’re compliant.
CCM eliminates this headache by continuously mapping vulnerabilities to compliance requirements. If a security gap could put your SOC 2 certification at risk, CCM flags it immediately, tracks remediation, and even automates reporting—so when auditors come knocking, you already have the answers.
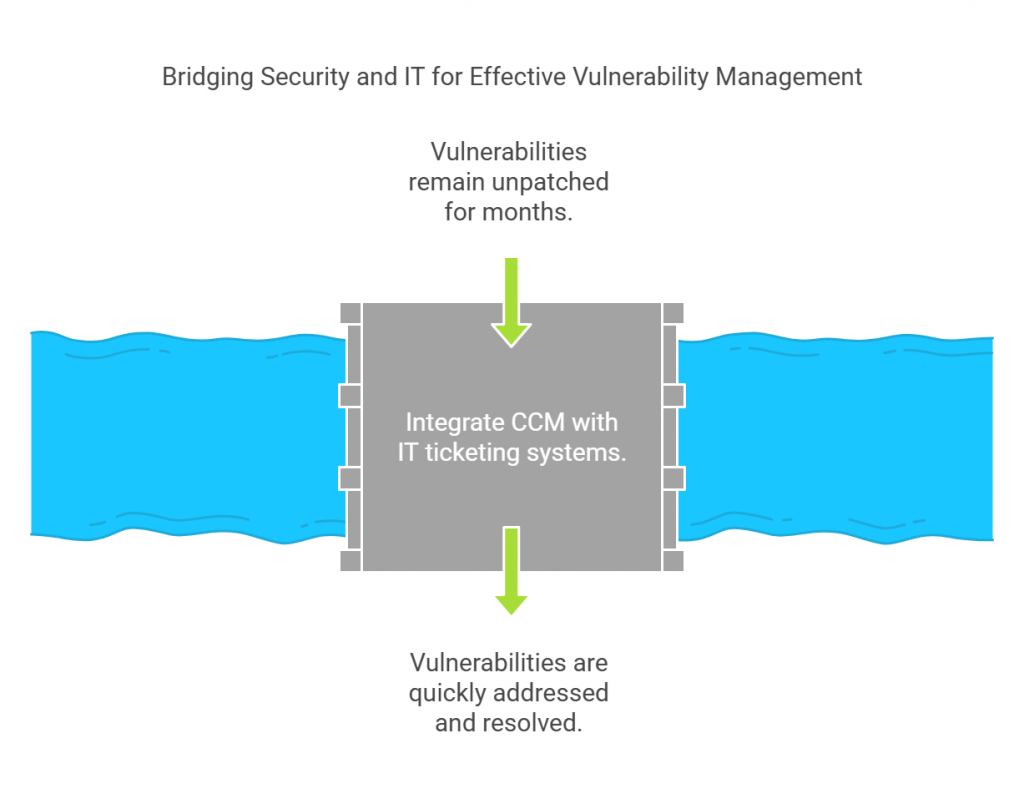
Fixing the Bottleneck Between Security and IT
One of the biggest problems in vulnerability management isn’t finding the vulnerabilities—it’s getting them fixed. Security teams identify issues, but IT teams are the ones who have to actually patch and remediate them. Without a smooth handoff, vulnerabilities sit unpatched for months, leaving organizations exposed.
The disconnect happens because VM tools often work in isolation from IT workflows. Security teams might generate reports and throw them over the fence to IT, but by the time remediation teams get to them, priorities have shifted, tickets get lost, and nothing happens.
CCM fixes this workflow breakdown by integrating directly with IT ticketing systems like ServiceNow and Jira. Instead of just generating reports, it:
- Automatically creates remediation tickets for high-risk vulnerabilities
- Assigns tasks to the right teams based on risk and urgency
- Tracks SLA compliance to ensure vulnerabilities don’t go unresolved
No more manual tracking. No more guessing what’s actually been patched. Just a smooth, automated process that ensures the most dangerous vulnerabilities get fixed first.
Adapting to New Threats, Not Just Yesterday’s Risks
The security landscape changes daily. What was considered a low-risk vulnerability last week could suddenly become high risk if a new exploit is released. VM tools operate on static risk models, which means they often fail to adjust to new threats.
CCM brings in real-time threat intelligence to keep security teams ahead of attackers. It continuously:
- Monitors global threat feeds to detect newly weaponized vulnerabilities
- Adjusts risk scores dynamically based on active exploitation trends
- Updates compliance mappings to reflect new regulatory changes
For example, if a zero-day vulnerability is discovered in an enterprise software you use, CCM doesn’t just wait for the next scheduled scan. It immediately alerts security teams, updates risk priorities, and generates an emergency remediation plan—all without manual intervention.
How SPOG.AI’s Audisphere Automates Vulnerability Metric Monitoring
SPOG.AI’s Audisphere platform takes CCM to the next level by automatically collecting, analyzing, and visualizing key vulnerability management metrics in real time. Instead of manually piecing together data from spreadsheets and reports, Audisphere provides a unified dashboard that security teams can use to monitor risk, compliance, and remediation progress.
Here’s how Audisphere helps organizations track and act on the right security metrics:
✔ Real-Time Asset Discovery: Automatically detects all assets, including on-prem, cloud, and third-party systems, ensuring that nothing goes unmonitored.
✔ AI-Driven Risk Prioritization: Goes beyond CVSS scores by prioritizing vulnerabilities based on threat intelligence, business impact, and compliance mandates.
✔ Continuous Patch Compliance Tracking: Monitors whether patches are applied on time and sends alerts for overdue vulnerabilities before they become security risks.
✔ Live SLA Monitoring: Tracks whether security teams are meeting remediation deadlines and provides automated reports to ensure accountability.
✔ Automated Compliance Audits: Maps security gaps to regulatory frameworks like ISO 27001, NIST, and PCI DSS, ensuring that organizations stay compliant without manual effort.
✔ Dynamic Risk Scoring: Continuously updates risk ratings based on active threat intelligence, so security teams can react before attackers exploit new vulnerabilities.

For example, if a zero-day vulnerability is detected in a critical business application, Audisphere can:
- Instantly update the risk score and flag the issue as high priority.
- Generate a remediation ticket in ServiceNow and assign it to the correct IT team.
- Track patch deployment progress and alert security leaders if remediation deadlines are missed.
- Update compliance reports automatically, ensuring that organizations remain audit-ready.
Why This Matters for Security Teams
By continuously tracking vulnerability management metrics, SPOG.AI’s Audisphere eliminates guesswork and helps security teams:
✔ See their security posture in real time instead of relying on outdated reports.
✔ Fix the most critical vulnerabilities first, based on actual risk rather than just severity scores.
✔ Speed up remediation workflows, ensuring that patches are applied before attackers can exploit them.
✔ Stay audit-ready by tracking compliance with ISO 27001, PCI DSS, NIST, and other regulatory standards.
✔ Reduce alert fatigue by filtering out low-priority vulnerabilities and focusing on high-impact security risks.
With CCM and Audisphere, organizations can stop reacting to vulnerabilities and start managing security proactively. Instead of scrambling to fix security gaps after an attack, security teams can use real-time risk intelligence to prevent breaches before they happen.
